Replies (36)
Nice one!
Is there much chatter on the anonymity aspects of nostr? Ofc downsides of decentralization is that servers can be controlled by malicious parties (expected e.g. hotlinking image assets to servers I control to IP dox people)
Yes I think it's important to a lot of people on nostr, that's why I had to ship Tor on day one basically. People are well aware I think
One caveot here: Clients do not have to AUTH with their own pubkey just to send a NIP17 DM though.. Only to receive. They do have to AUTH, but it can be with any key.. At least, that's how I have it setup. Unsure about the other relay solutions. The receiving side is where the relay attempts to 'protec', by only sending DMs that were intended for who is authing. Any other relay, that does not have auth, will just send all of them from everyone to anyone, waiting to be decrypted in the future if one of the keys is p0wned.
The other reasons AUTH is good is that if you're using a relay that is trying to provide you a solid service, like an aggregator relay, or a custom feed relay.. These you will notice because you are a 'customer' of them, and AUTHing puts you ahead in the queue on a busy relay by increasing your limits.
Anyway, that's my speil on why AUTH is not just for doxing. It's hard to implement and so I think devs tend to talk only about it's downsides. I think you're on the right track here with the wisp tho! Thank you for giving people options to AUTH.
Yep you make good points, for relay feeds a one time authorization to view the feed and remember auth preference I think is a good middle ground.
whats that little damus icon?
The relay my dm was found on
ah nice. cool idea
@KernelKind (idea stealing activated)
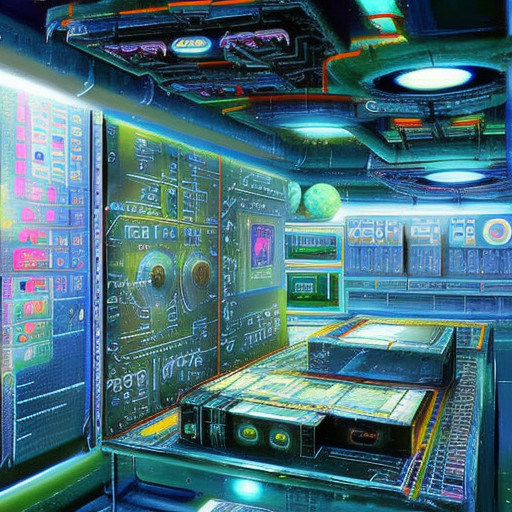
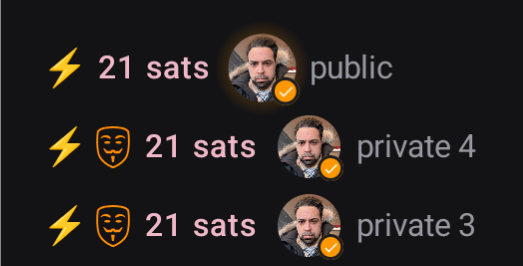
Please steal my private zap idea!
A zap request only sent to sender/receiver DM relays and hope user has selected auth relays
Fair point—day one's the right call for that. What made you prioritize it over other privacy layers initially?
we already have a private zap spec
Not sure if amethyst just didn't implement it correctly, but the zaps are still public, just anonymous 😭 need to ensure CRA can't see it, but recipient knows who sent it... Is that how spec works?
Is this live on Damus? Do you know if most zap wallets support this anon tag?
doesn't require any custom support from zap wallets. this has been live since like 2023
Ok thx sir implementing it. But will keep it as only sending to dm relays for extra cypherpunk
It’s all kinda confusing. And I’m pretty technical. What I read today says what I read yesterday isn’t the right way. Every day.
Do you have public messages?
autoplay in wisp is a nightmare when scrolling through profiles which only post videos. it plays 2 or 3 at a time
Hmmm yes fair point, I will fix this
A good client, will look at the combination of kind 10050 relay lists. If alice and bob both have a DM relay in common Auth to it with your key. Then, if bob is sending to alice's extra relays, then auth with the ephemeral key that was generated and send the event without making any reqs... (after auth handshake). Seems ez 😁 You won't be keeping that connection anyway it was one time use for sending.
I am not sure about this, because it undermines privacy in other ways. Now, if I want to protect my privacy by enforcing auth on my outboxes (to restrict reads to people I follow or something), I am banning myself from wisp. Better would be to have some kind of heuristic for relays that might legitimately enforce auth. If someone I follow has a relay that enfoces auth, I don't mind identifying myself. But if I'm browsing topics or whatever that changes.
@hzrd149 I appreciate your experiment but I think auto auth is not the enemy. Fingerprinting can happen in many other ways. It's worse on nostr, but it's also true of the entire rest of the internet.
Outbox has been my soapbox on privacy tangential to this. If I have to auth to 100s of relays is even worse than just telling 2-3 providers who likely already know me based on my activity.
my strfry router is handling 90% of my outbox usage, it is unable to auth, and that's probably why I didn't make "the list" 😂🦅🏝️
outbox reading that is. for writing, i will auth to whoever im replying to or zapping if it requires it via RT-android.
if you don't pay them. sure
even though your fucking reqs are gonna have your npub all over it, repeatedly. but don't mind me
if you pay them why did you pay them if you don't trust them to respect confidentiality?
maybe you shuoldn't use 100s and maybe pick one you fucking trust.
i'm so fed up with people thinking that authing is any worse than askiing for your own DMs which anyone can also fetch and see the fucking timestamps. because the relay didn't require auth it can't stop them.
> maybe you shuoldn't use 100s and maybe pick one you fucking trust.
That's my point. Most client's "force" outbox by default. In my case I've had to use uBlock origin to restrict that.
You just repeated what I said
probably doesn't affect me because of my popularity m the church of nostr freedumb. many publish fails. good call, actually. gonna make a toggle.
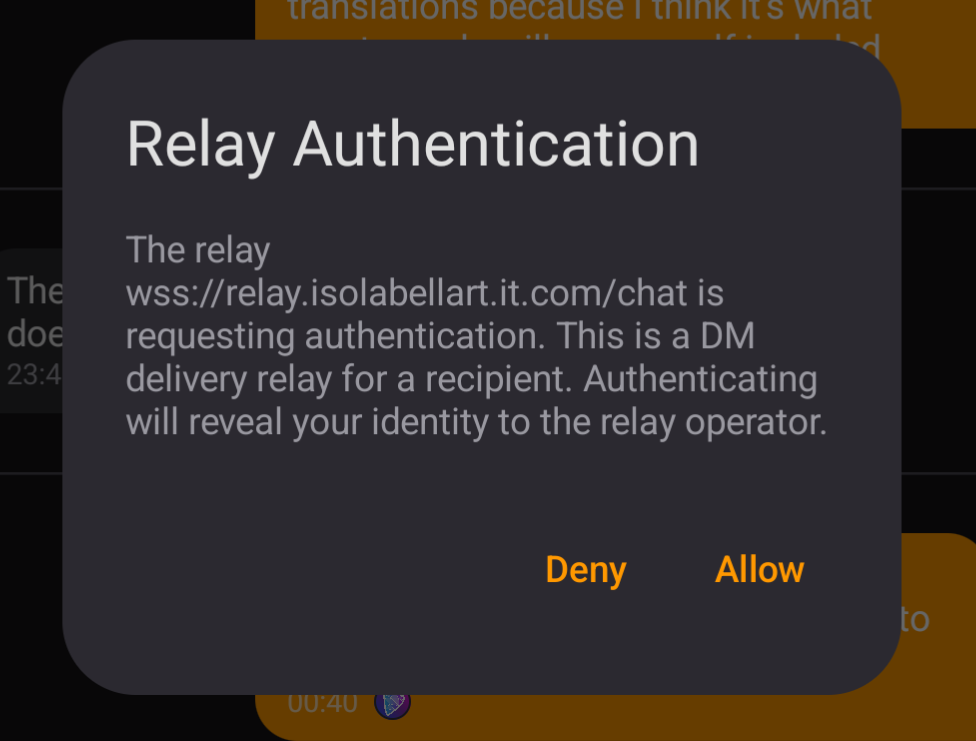
I respectfully disagree but not because of the fingerprinting, even though its worse on nostr then google analytics. but because when apps push users to sign NIP-42 indiscriminately they are effectively pushing the user to give full control of their nsec over to the app, presuming the user clicks "approve all".
The best thing the user can do with these apps is select "approve all relay auth" but nothing else. but then we are left here where the client the dox the user to any relay they happen to connect to.
Kind-based approvals is a broken UX pattern. I don't know what better would look like, but no way is a user going to know offhand what kind 68291 is. I also don't think it's realistic for signers to render every kind correctly either. Honestly I feel like developers of signers have sort of dropped the ball on exploring better ways to reconcile UX smoothness with user safety/privacy/control.
@greenart7c3 have you thought about parsing relay AUTH events to approve/reject/remember them by relay in amber? Would be a worthy feature I think given how common this pattern is.
Real tag
@greenart7c3
(Did you use wisp btw)
Already in there in the latest version, if you setup it to auto approve before you need to change it in amber. Didn't want to break the experience for anyone
🎉🎉🎉🎉🏆🏆🏆🏆