Thankfully the fake Wisp publisher doesn't seem to have malicious intent, and was done moreso by accident than on purpose. However this does kick up a whole bunch of questions for
@Zapstore:
- Shouldn't there be some kind of manual approval when app names collide with pre-existing ones?
- How can you let a different publisher publish an app with the same ID `com.wisp.app` as a pre-existing, trusted package from the original dev
@utxo the webmaster 🧑💻 ?
- There are literally zero flags/alerts/warnings on the interface when browsing this duplicate app.
Another example is Cake Wallet
@Cake Wallet, for the past few versions Google has flagged this as a malicious app (it wasn't the case before), so I have avoided upgrading, even though I originally installed the zapstore version. If it's not fixed soon I will have to uninstall then re-install via Play or another market (annoying as then a full re-sync is required).
To date I have enjoyed using zapstore, but I feel like this is a great lesson learned to tighten up some of the security measures so we maintain high trust in what is published there.
View quoted note →







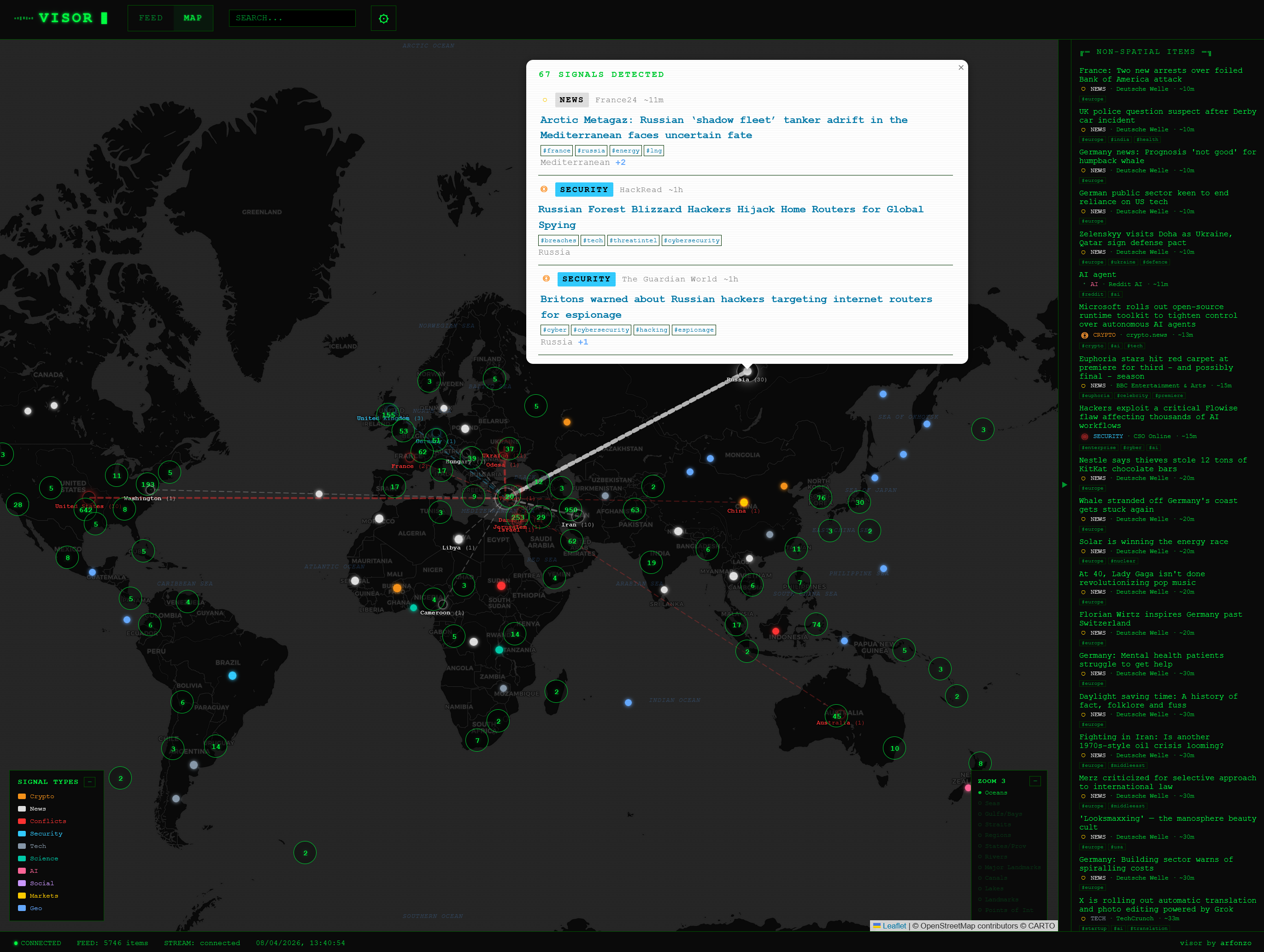
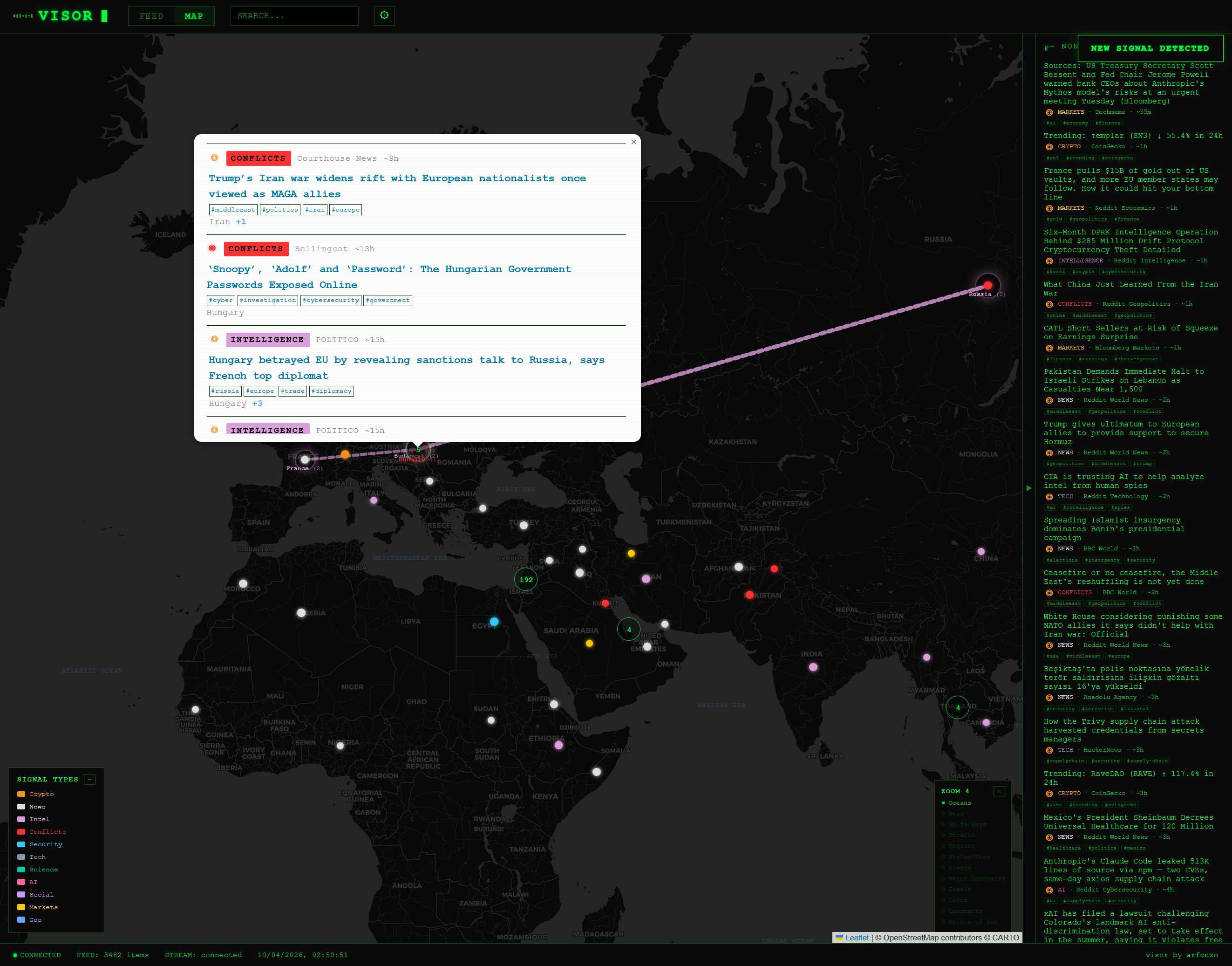 Having fun with my private #OSINT project, visor.
Having fun with my private #OSINT project, visor.