#OPSEC365 025/365
A Surveillance Detection Run is standard methodology.
A proper SDR uses deliberate direction changes, speed variations, and chokepoints force anyone following to reveal themselves or break contact. Intelligence officers run them before every sensitive meeting. The route needs at least two direction changes to draw in surveillance.
Design your SDR like a professional: identify two or three chokepoint locations - a narrow entry, a cafe door, a transit turnstile - where anyone behind you must commit. Vary your pace. Stop naturally at a shop window and use the reflection.

Sam Bent
contact@sambent.com
npub1y7rv...d0r3
Agorist. Counter-economist. Privacy maximalist. Student of OPSEC. Anti-authoritarian. Free speech absolutist. Logician. Ex-Darknet Vendor. Youtuber.
The state will always side with the franchise over the independent because the franchise pays lobbyists.


#OPSEC365 024/365
Every Word document and PDF you create embeds your name, your computer's name, edit history, and sometimes the file path showing your folder structure.
Before you send a document to someone you don't fully trust, that metadata tells them more about you than the content does.
Right-click a document you've shared recently, check Properties or Get Info, and see what's embedded.
ExifTool strips metadata from documents and images. MAT2 handles batch cleaning. For quick fixes, Save As to a new file often drops edit history, and printing to PDF can strip some metadata. Check your work before sending.
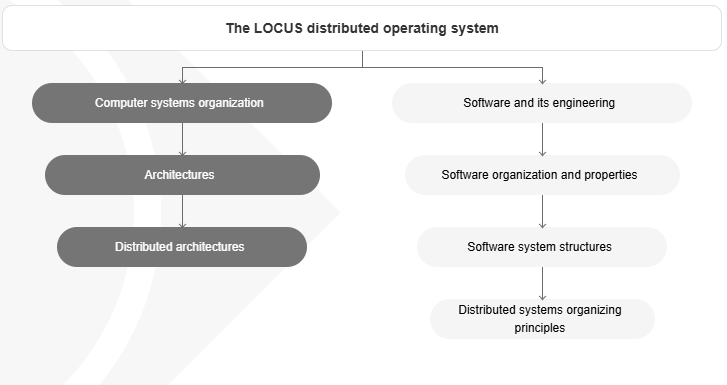
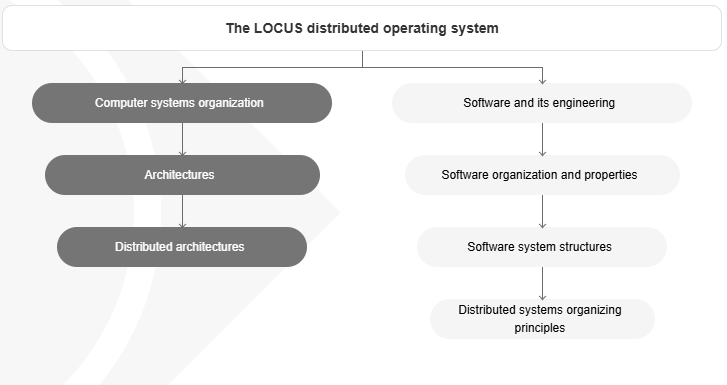
Virtualization security and hypervisor isolation mechanisms.
"Virtual machine monitors must provide strong isolation between guest operating systems."
- 𝗣𝗿𝗼𝘁𝗲𝗰𝘁𝗶𝗼𝗻 𝗠𝗲𝗰𝗵𝗮𝗻𝗶𝘀𝗺𝘀 𝗶𝗻 𝘁𝗵𝗲 𝗩𝗠/𝟯𝟳𝟬 𝗛𝘆𝗽𝗲𝗿𝘃𝗶𝘀𝗼𝗿 by R.J. Creasy (1981)
https://dl.acm.org/doi/10.1145/800217.806615
#OPSEC365 023/365
In 2018, Strava's global heatmap revealed the locations and layouts of secret military bases because soldiers were tracking their runs.
Fitness apps broadcast where you exercise, what routes you take, and what time you're usually there. If your profile is public, anyone can see your patterns.
Strava's default is public. Soldiers exposed military base layouts in 2018 because nobody changed it. Set your fitness profiles to private.
Strava, Garmin Connect, Apple Fitness, and Nike Run Club all have privacy settings buried in menus. Set profiles to private, disable activity sharing, and consider whether you need GPS tracking at all for workouts near your home.
#OPSEC365 022/365
JP 3-13.3 OPSEC doctrine defines a Critical Information List — data whose disclosure degrades operational security. Your home has one too.
Every smart speaker expands that CIL to a corporate entity you never vetted. Bedroom. Home office. Kitchen. Each room is a compartment. Each speaker collapses it.
Hoepman's SEPARATE strategy: isolate actors from their data proxies. The fix is removing the device from sensitive contexts entirely.
Apply need-to-know at the room level. Your home office — work calls, finances, health discussions — has no operational reason to be audible to an Amazon server. Physically separate listening devices from high-sensitivity contexts.
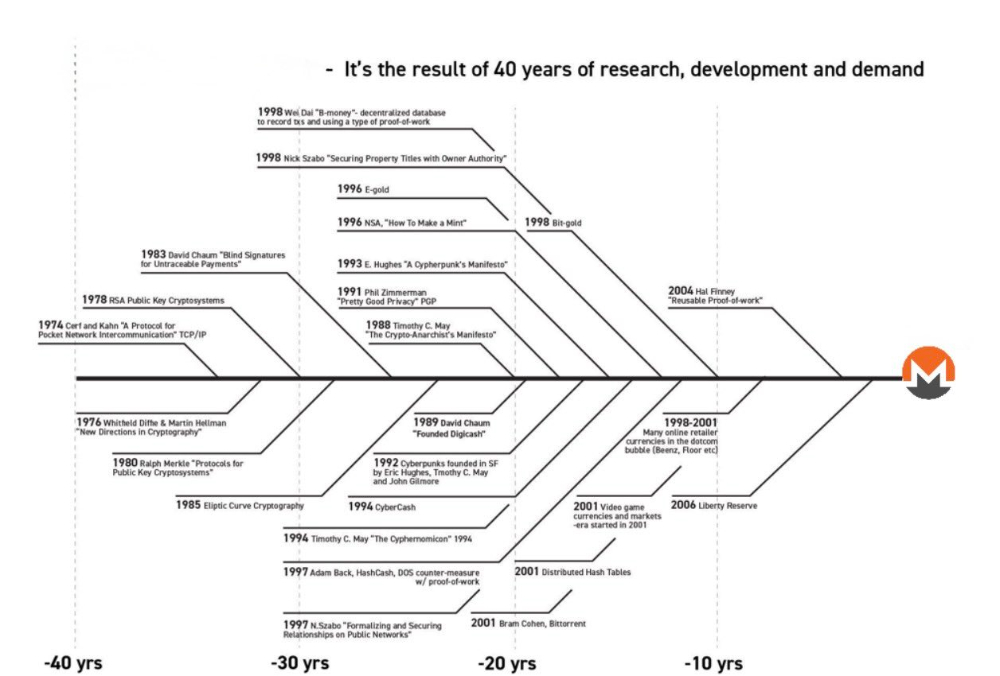
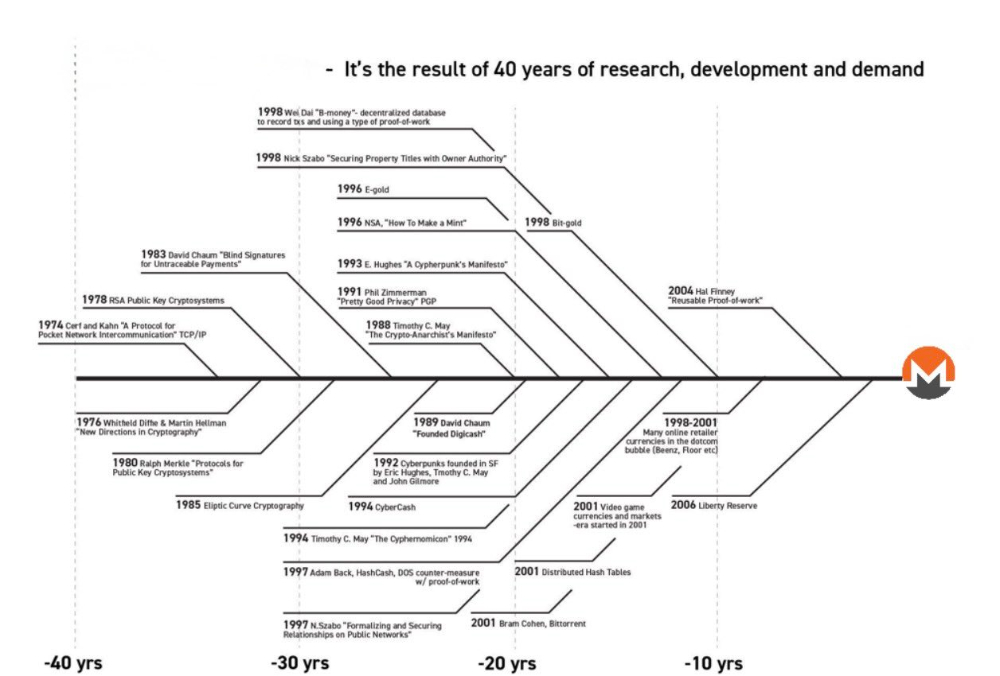
Monero didn't come from a whitepaper and a marketing team,
it's the direct descendant of four decades of cypherpunk work from Chaum, Zimmermann, May, Back, Finney, and Szabo,
built by people who actually read their papers.
#OPSEC365 021/365
OPSEC Step 2 is threat analysis: research your adversary's actual collection capabilities. Public records, court databases, social media aggregators, data brokers, and reverse image search form a surveillance infrastructure anyone can access for under $50/month.
Your adversary doesn't need hacking skills. They need patience.
NTTP 3-13.3 lists adversary collection as HUMINT, SIGINT, OSINT, GEOINT, and MASINT. For most civilians, HUMINT and OSINT are the primary threats. Digital countermeasures alone fail if your adversary collects via human contact.
#OPSEC365 020/365
Who knows you're traveling before you leave?
The coworker you told about your trip, the auto-reply announcing you're out of office, the social post about your upcoming vacation. Each one widens the circle of people who know your home will be empty.
Next trip, try keeping the details vague until you're back and see who actually needed to know.
Auto-replies don't need to say where you're going or when you'll be back. Having limited email access and responding when available reveals nothing. The same applies to telling acquaintances your travel plans versus just saying you're busy that week.
darkwebdaily.live update — new sites added across the board, most pulled from tor.li.
NEW: AI SECTION (don't use these — run local AI instead)
- Water AI
- Dig AI
FORUMS
- Qubez
- Tenebris
- Cloak
- TorChat
- KHAZAD
- Ark Forum
- NZ DN Forum
- OnionSpace
- Secret Garden
MARKETS
- Allure
- FawkesMarket
NEWS
- BBC
- DarkDotWeb
- DarkHub
INFO / SECURITY
- OnionArchive
- Null World
- Kikuri
CRYPTO
- b1eXch
- SageSwap
- Trocador
- Ask&Bid
- FairTrade
TOOLS
- Dump.li
- DreadPirate
- MixTum
REMOVED (dead/consolidated)
- Impact, Kerberos, Cocorico, Lion (markets)
Also: every onion link now opens in a new tab, and the RECOMMENDED ribbon moved to the bottom-right of each card.
darkwebdaily.live
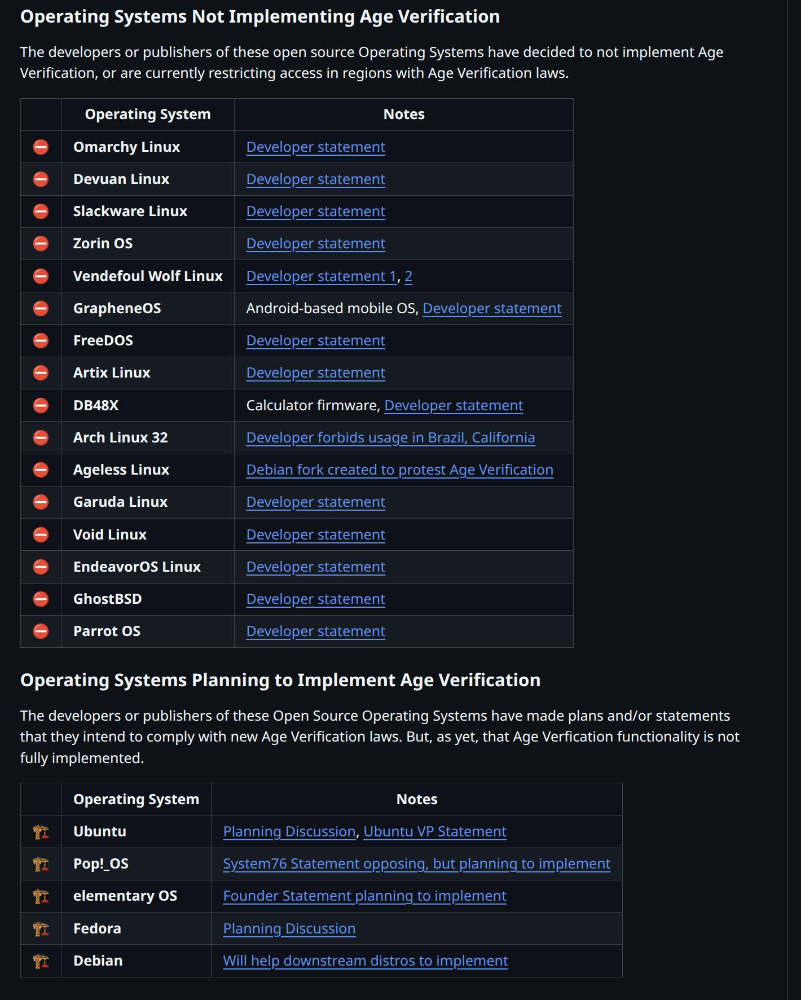
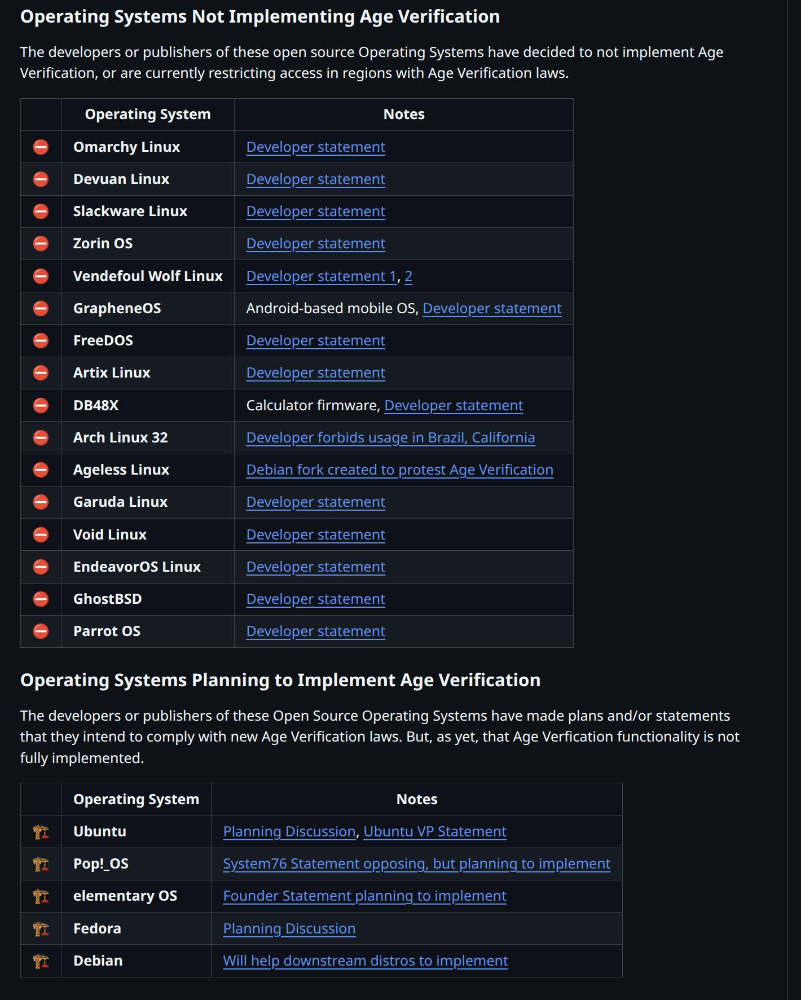
The fact that the first list is longer than the second list by itself is actually kind of reassuring.
The fact that we even need these lists is pathetic.
#OPSEC365 019/365
Photos of your home reveal more than you think.
That Zoom background shows your bookshelf, your art, the view from your window. The photo of your new couch includes the street visible through the curtains. Each detail helps someone build a picture of where and how you live.
Before you post your next indoor photo, scan the frame for what you didn't mean to include.
Blur backgrounds in video calls when possible. Before posting indoor photos, check what's visible in reflections, windows, and background details. Real estate listings and social media posts have been used to case homes for burglary because people forget what's in the frame.
Renovated DarkwebDaily.Live with a fresher UI.
Added 'a'statistics' page too.
Use the above url or the onion:
http://dailydwusclfsu7fzwydc5emidexnesmdlzqmz2dxnx5x4thl42vj4qd.onion/
No JS.
"Tainted coins" is a concept that only exists when your blockchain snitches on transaction history.


#OPSEC365 018/365
Before picking a single countermeasure, OPSEC doctrine requires you to profile your adversary. A stalker uses HUMINT. A data broker uses OSINT at scale. A state actor adds SIGINT and GEOINT. These are not the same threat.
Treating them identically is how people waste effort protecting against the wrong attack.
Shostack's threat modeling framework asks: realistic attackers vs you specifically? The Verizon RISK A4 model categorizes actors by Actors, Actions, Assets, and Attributes. For personal OPSEC: map adversaries to their most collection methods before choosing any countermeasure.
#OPSEC365 017/365
Talking on the phone in public means everyone around you is in the meeting.
The coffee shop hears your business deal. The airport gate hears your medical results. The elevator hears you confirming your address to the delivery service. You assume nobody is paying attention, but someone always is.
Next time you're about to take a call in public, glance around and notice who would hear it.
If you have to take a sensitive call in public, keep it vague and finish the details later. Saying you'll send the specifics reveals less than reading your SSN out loud to the insurance company while standing in line at Starbucks.
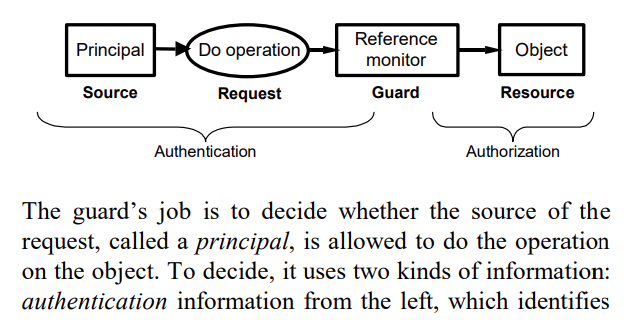
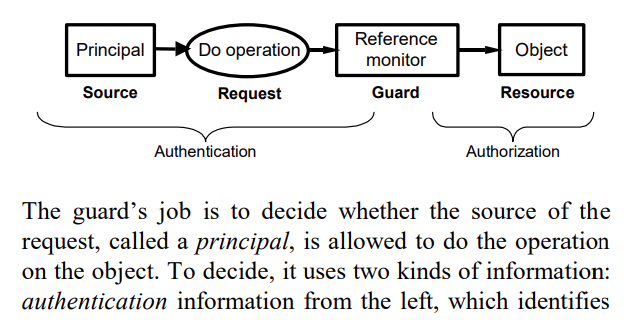
Ken Thompson's acceptance speech for the Turing Award on security thinking.
"The moral is obvious. You can't trust code that you did not totally create yourself."
- 𝗖𝗼𝗺𝗽𝘂𝘁𝗲𝗿 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗶𝗻 𝘁𝗵𝗲 𝗥𝗲𝗮𝗹 𝗪𝗼𝗿𝗹𝗱 by Butler Lampson (2004)
https://www.microsoft.com/en-us/research/wp-content/uploads/2004/06/Computer-Security-in-the-Real-World.pdf
#OPSEC365 016/365
The military calls it a Critical Information List. Step one of OPSEC starts with identifying exactly what information, if collected by your adversary, would degrade your ability to operate safely.
Most people skip this step and jump straight to countermeasures they don't actually need.
Start your personal CIL with three columns: what you want protected, who could weaponize it, and how they'd likely obtain it. Military doctrine (JP 3-13.3) defines critical info as answers to key questions your adversary is actively trying to answer.
Name one other service where the provider threatens you with prison for refusing to pay.
#OPSEC365 015/365
Every package you order creates a record linking your name to your address.
That Amazon order, that supplement you'd rather keep private, that gift that reveals your relationship status. Somewhere there's a database connecting your identity to your home and your purchasing habits.
Most of them don't need it. They asked because you gave it.
A PO Box or private mailbox service breaks the link between your name and home address for most deliveries. It costs around twenty dollars a month and keeps your physical location out of dozens of corporate databases that will eventually get breached.