This is a tablet PC with Cellebrite UFED, a mobile forensics acquisition software. Users plug a target device into it where it then will attempt to extract as much data on the device as possible. The software on the laptop is Physical Analyser which is for forensic analysis.
This video is dated, and Cellebrite UFED's UI, logo and capabilities have changed a lot since the video was released. This tool is also not exclusive to UK law enforcement and there are also competitor solutions, which many countries around the world use plus the competitors.
Cellebrite sell a variant of this product named Cellebrite Premium. The difference to standard UFED and Premium is that Premium comes with wider device extraction support through zero-day exploits. As described it also allows extraction of vulnerable devices that are locked.


This business model is not exclusive. XRY Pro (MSAB) and GrayKey (Magnet Forensics) are other exclusive forensic tools. Cellebrite are the second-oldest of the three companies (on joining the forensics market) but are one of the most capable thanks to their funding and location.
How and if these tools are able to extract your device's data depends on:
- The device you are using
- The installed OS and version
- The lock state of the device
- Configured security settings of the device
- Strength of your phone's unlock credential
For a locked device exploiting security vulnerabilities is required to extract data almost all of the time. There are two different device lock states on Android and iOS: After first unlock (AFU, Hot) and before first unlock (BFU, Cold). This is due to how encryption works.
Modern Android and iOS encrypt all users' data by default with keys derived from the user's credentials. When a device is unlocked once, data is no longer encrypted at rest and is accessible during that boot session. When a device is BFU, all sensitive data is at rest.
Data not being at rest provides more OS attack surface to exploit bypassing lock screens or other measures and access to the data without needing the original PIN/password to decrypt it. For BFU devices brute forcing is required to decrypt data first and the only data not encrypted is a minimal footprint of the OS used for unlocking the device and global OS configuration and metadata.
To make extraction impossible make sure your device is powered off and you use a secure, high-entropy passphrase before seizure. GrapheneOS provides a configurable, automatic inactivity reboot feature.
We also provide several other countermeasures to these tools as well. GrapheneOS locked devices as a whole is unsupported by Cellebrite.
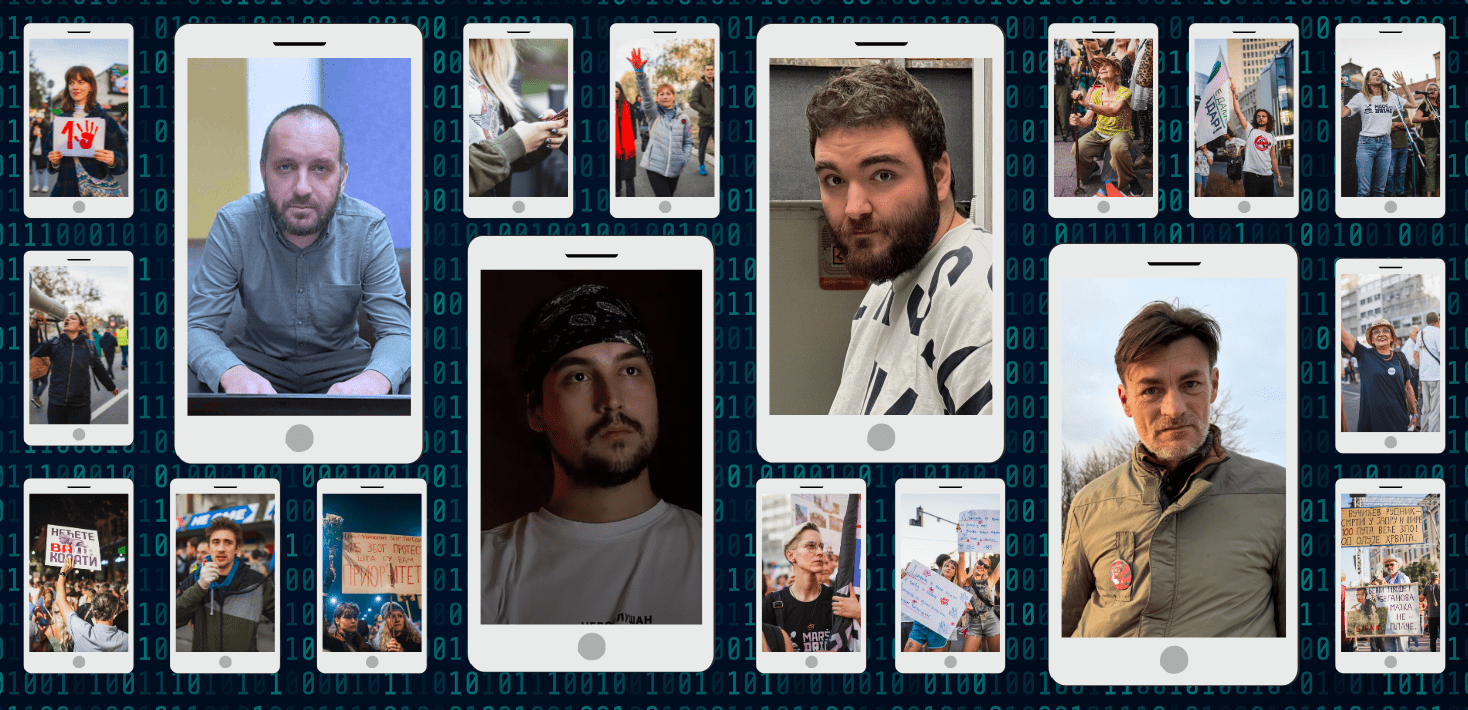
If you are an opposition activist in a high-risk country you should be concerned about potential attacks from such tools. They have been abused to target activists in numerous countries like Serbia and Jordan.

The Citizen Lab
From Protest to Peril: Cellebrite Used Against Jordanian Civil Society - The Citizen Lab
Through a multi-year investigation, we find that the Jordanian security apparatus has deployed forensic extraction products manufactured by Cellebr...
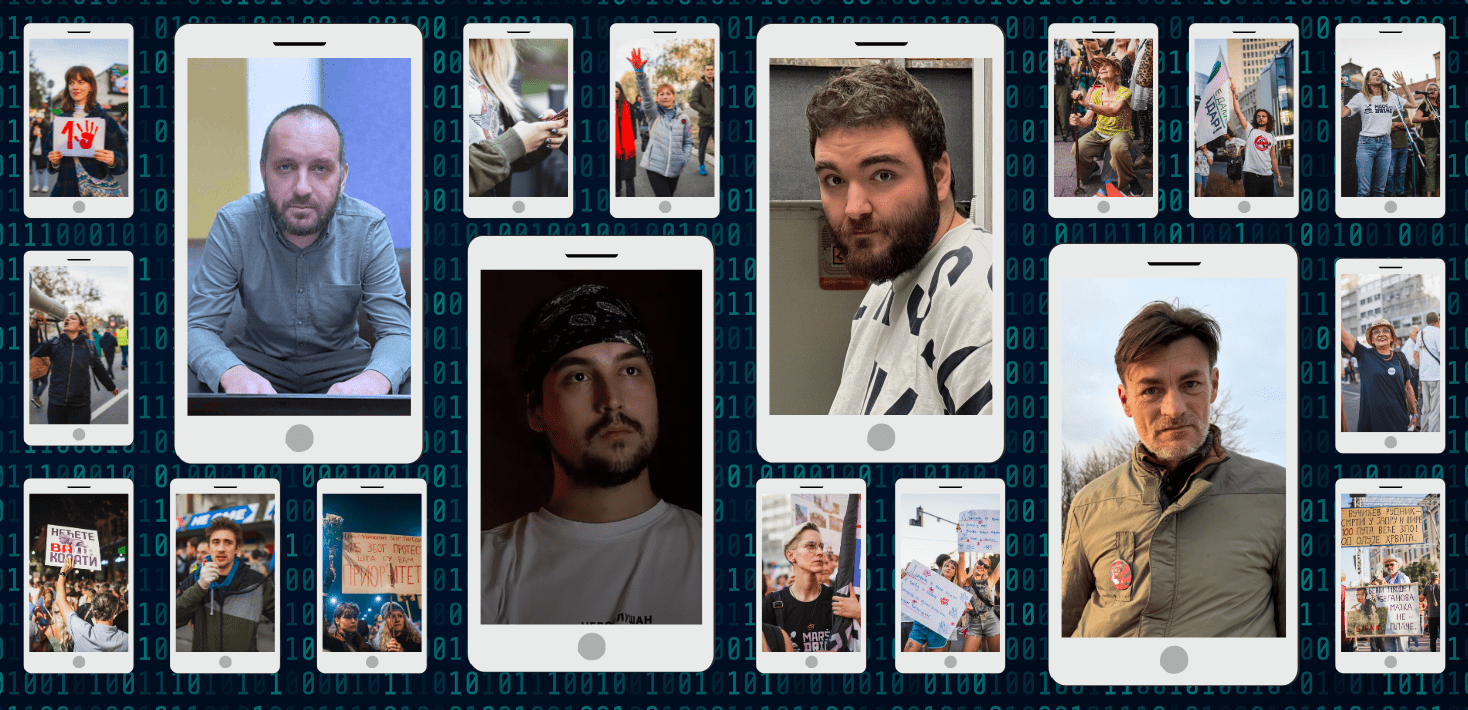
Amnesty International
Serbia: Authorities using spyware and Cellebrite forensic extraction tools to hack journalists and activists
Serbian authorities are using spyware and Cellebrite forensic extraction tools to hack journalists and activists in a surveillance campaign.
Despite if a business claims this use of their product like this is unauthorised, it doesn't change the fact that they will be used like this again, that they don't know about it until after it has violated someone's rights and that the security vulnerabilities remain unpatched.
GrapheneOS provides an auto-reboot to put data at rest, a USB-C port control to disable data transfer or the port entirely when booted into the OS, clearing sensitive data of memory and exploit protection features.
View quoted note →