#OPSEC365 015/365
Every package you order creates a record linking your name to your address.
That Amazon order, that supplement you'd rather keep private, that gift that reveals your relationship status. Somewhere there's a database connecting your identity to your home and your purchasing habits.
Most of them don't need it. They asked because you gave it.
A PO Box or private mailbox service breaks the link between your name and home address for most deliveries. It costs around twenty dollars a month and keeps your physical location out of dozens of corporate databases that will eventually get breached.

Sam Bent
contact@sambent.com
npub1y7rv...d0r3
Agorist. Counter-economist. Privacy maximalist. Student of OPSEC. Anti-authoritarian. Free speech absolutist. Logician. Ex-Darknet Vendor. Youtuber.
Most Tor Docker images are running outdated Tor, no guard protection, and leave telemetry on by default.
HiddenForge v2.0.0 (my creation):
Tor 0.4.9.6 + Vanguards,
every dependency SHA256-pinned,
zero telemetry,
read-only filesystem,
rootless Podman support.
Built for a state-level adversary threat model.


GitHub
GitHub - DoingFedTime/HiddenForge: Hardened Tor hidden service container. Runs Tor 0.4.9.6 with Vanguards guard protection on Alpine 3.23. Designed for a state-level adversary threat model.
Hardened Tor hidden service container. Runs Tor 0.4.9.6 with Vanguards guard protection on Alpine 3.23. Designed for a state-level adversary threat...
doingfedtime/hiddenforge - Docker Image

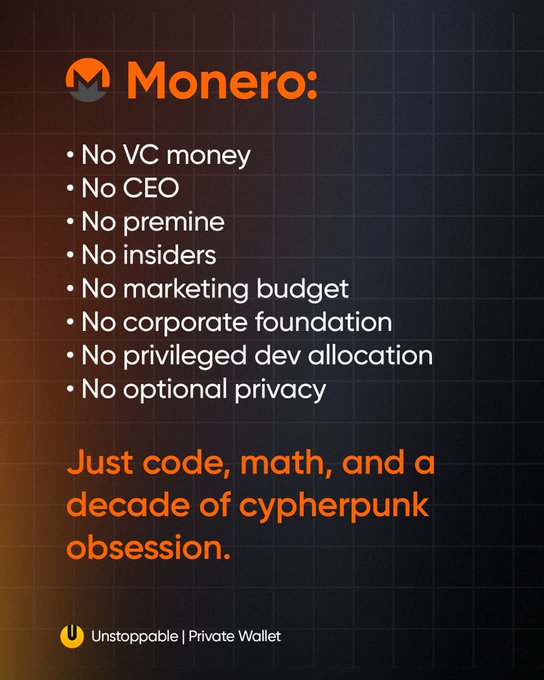
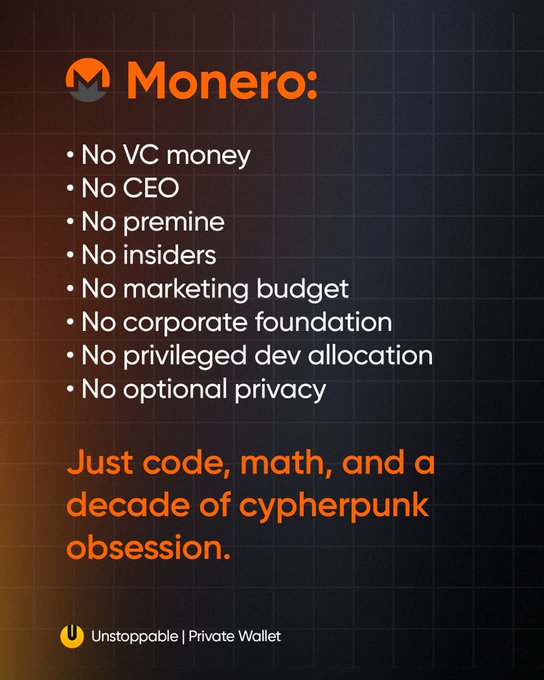
Monero has survived ten years on donations and volunteer labor while VC-backed "privacy" projects burned through millions building compliance tools,
turns out you don't need a marketing budget when the product actually works.
#OPSEC365 014/365
Who has a key to your home right now?
Family members, the ex who never returned theirs, the neighbor watching your place while you travel, the cleaning service, the property manager. Each one is a potential entry point you don't control.
If you can't name every person with access, you've already lost track.
Re-keying is cheaper than replacing entire locks and takes about fifteen minutes per door. If you've lost track of who has copies, it's worth the cost to reset the access list. Smart locks with revocable codes solve this for new access but create their own attack surface.
#OPSEC365 013/365
Alcohol removes the filter between what you know and what you say.
The classified project you're working on, the friend going through a divorce, the coworker you can't stand. After a few drinks, those things slip out to whoever happens to be sitting next to you at the bar.
Next time you're out drinking, notice what you almost said and what stopped you from saying it.
Professional intelligence officers target bars and social events specifically because people talk more freely there. If you work with sensitive information, consider who might be listening when your guard is down and adjust your drinking accordingly.
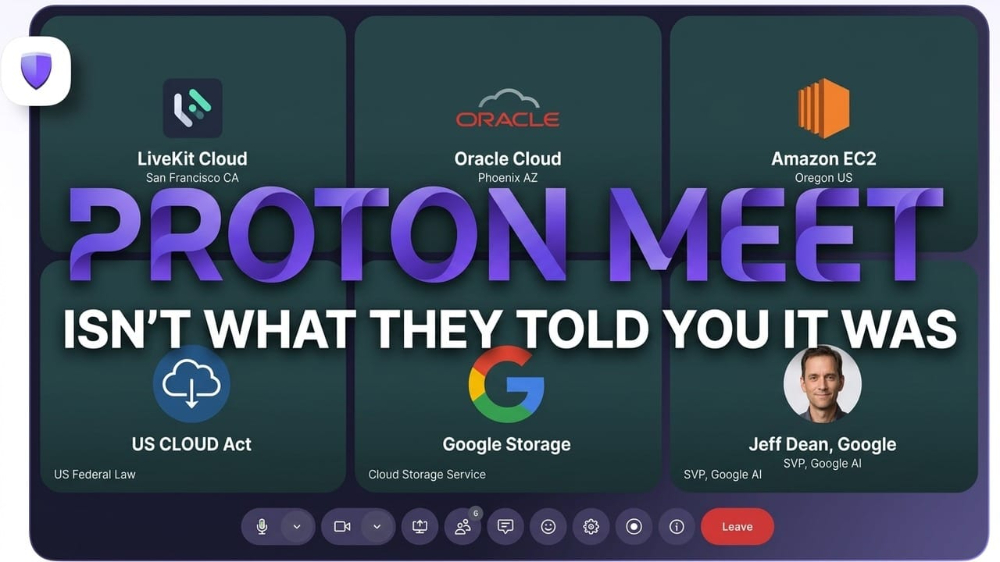
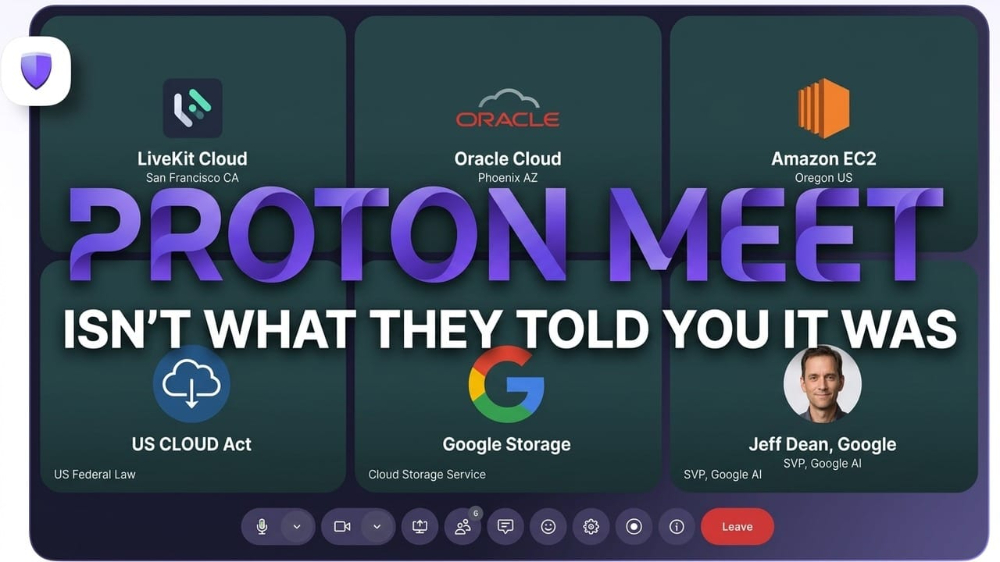
Proton built Proton Meet to escape the CLOUD Act.
They built it on CLOUD Act infrastructure.
Their website promises "not even government agencies" can access your calls.
The company routing them hands your call records to the government when asked.


Sam Bent
Proton Meet Isn't What They Told You It Was
Proton built Proton Meet to escape the CLOUD Act. They built it on CLOUD Act infrastructure. Their website promises "not even government agencies" ...
#OPSEC365 012/365
Your car tells people more about you than you realize.
The parking permit reveals where you work. The bumper stickers broadcast your politics, your kids' schools, and the gym you go to. The pattern of where you park and when tells anyone watching exactly where you'll be tomorrow.
Look at your car like a stranger and count how many facts they could learn from it.
You don't need to strip your car bare, but consider what each sticker or accessory reveals. The honor student bumper sticker just told a stranger your child's school and approximate age. The parking permit narrows down your employer. Each one is a piece of a puzzle.
Finally, an honest warning label about what financial privacy actually threatens.
#OPSEC365 011/365
Google your full name in quotes and see what comes up.
Data broker listings, old forum posts, voter records, that 10K you ran in 2014. Most people have no idea how much of their history is indexed and publicly searchable by anyone who wants to find it.
Whatever shows up on page one is what your adversary finds first.
Services like DeleteMe and Privacy Duck can remove you from data broker sites, but they're not perfect. The free version is doing it yourself by finding the opt-out page for each broker and submitting removal requests manually. It takes time, but it works.
Congress forced telecoms to build surveillance backdoors in 1994.
Chinese hackers found them.
The government's response is to ban your router.


This week Apple pulled VPN apps in Russia at Roskomnadzor's request
and forced UK users to hand over government ID to keep using their phones normally.
Sam Bent
Apple Obeyed Russia and Britain in the Same Week
This week Apple pulled VPN apps in Russia at Roskomnadzor's request and forced UK users to hand over government ID to keep using their phones norma...
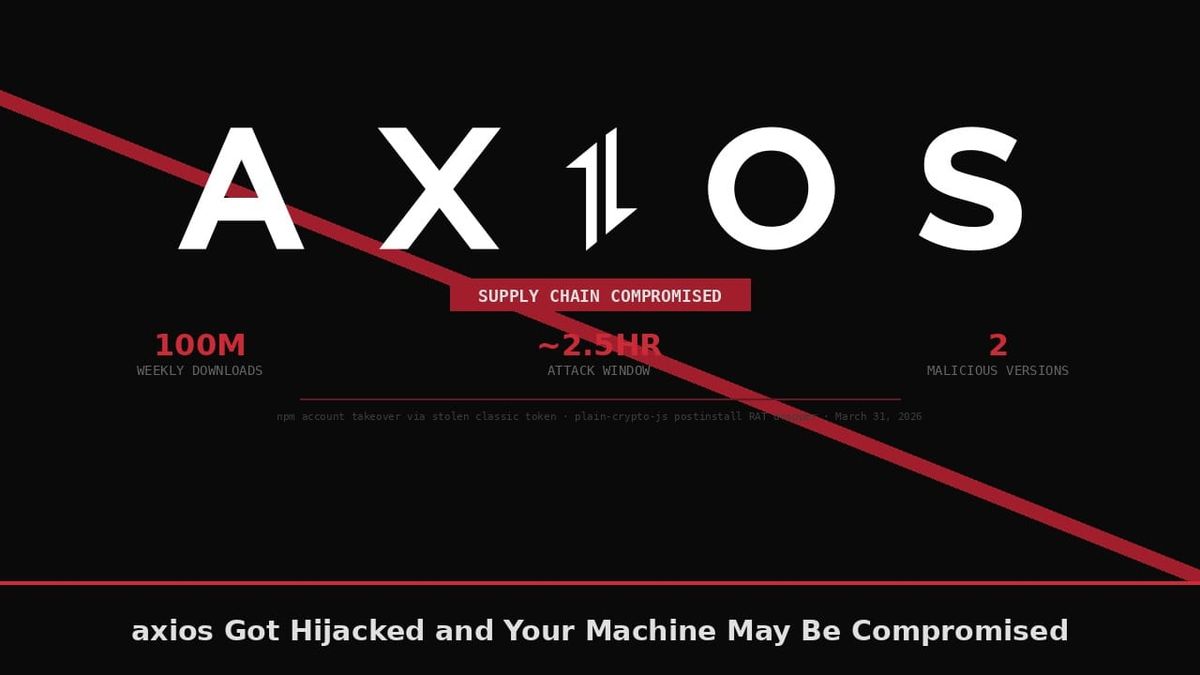
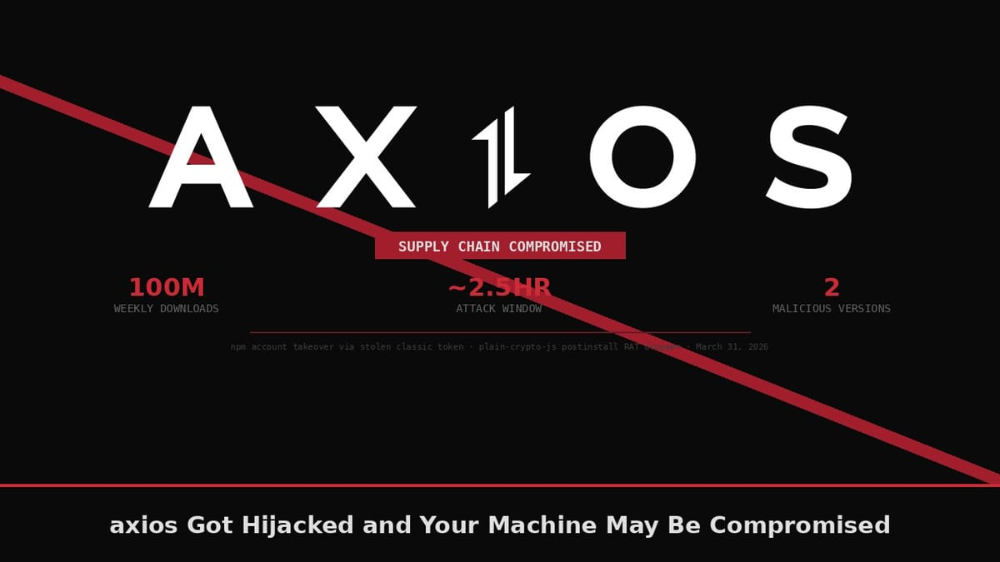
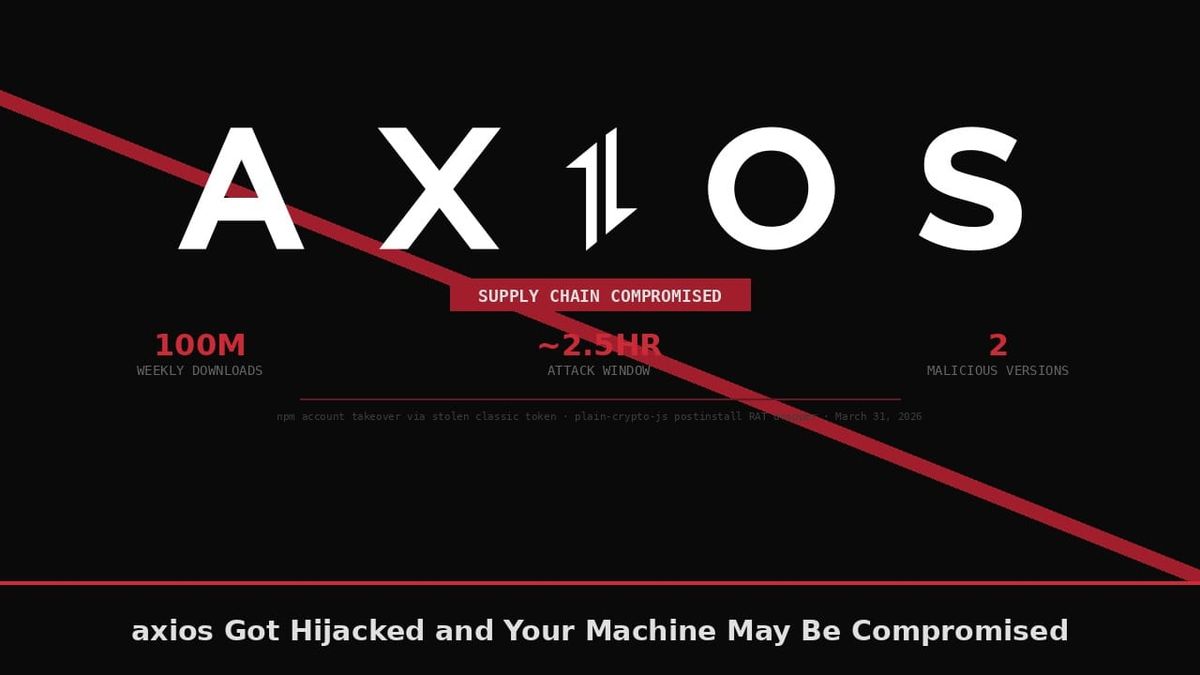
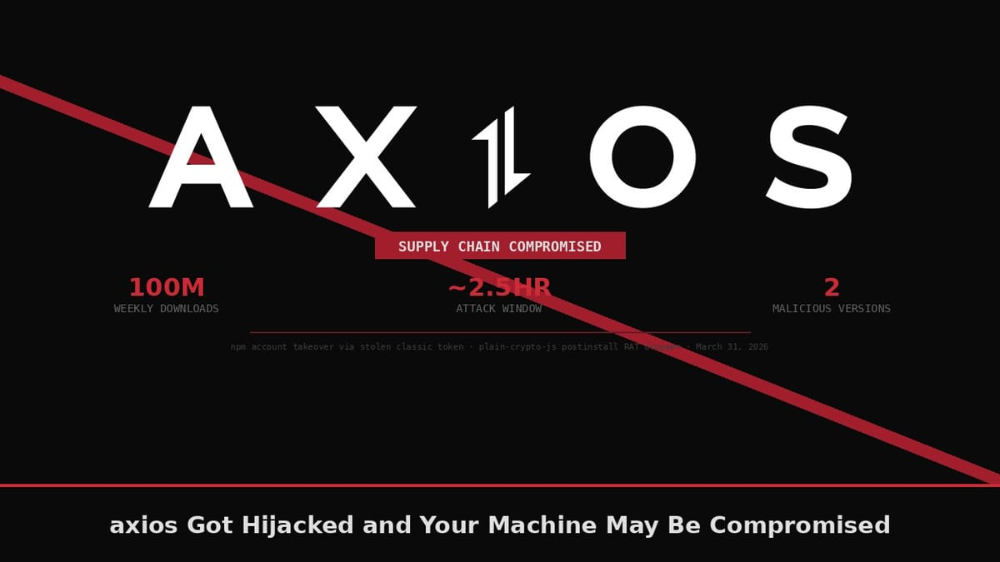
axios Got Hijacked and Your Machine May Be Compromised
Sam Bent
axios Got Hijacked and Your Machine May Be Compromised
A stolen npm token was all it took to poison axios, the package with 100 million weekly downloads, and drop a cross-platform RAT on every developer...
#OPSEC365 010/365
Your phone logs every call you make, every text you send, and the duration of each conversation. Even with encrypted messaging, your carrier knows who you contacted, when, and for how long.
Pull up your call history and imagine someone trying to map your relationships based purely on who you talk to and how often.
The connections are already logged.
Content can be encrypted, but metadata often can't. Who you call, when, and how often creates a pattern that reveals relationships, habits, and associations without anyone reading a single message. The structure of your communications tells its own story.
Anon, Feds hate you, it's not just a meme.
𝗔𝗹𝗶𝗰𝗲 𝗠𝗮𝗿𝗶𝗲 𝗝𝗼𝗵𝗻𝘀𝗼𝗻 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲 + 𝟮𝟱 𝘆𝗲𝗮𝗿𝘀
Relaying phone messages in a cocaine conspiracy.
First arrest ever.
𝗪𝗲𝗹𝗱𝗼𝗻 𝗔𝗻𝗴𝗲𝗹𝗼𝘀 | 𝟱𝟱 𝘆𝗲𝗮𝗿𝘀
Three sales of $350 worth of marijuana with an alleged ankle holster.
No prior record.
𝗗𝗶𝗰𝗸𝘆 𝗝𝗼𝗲 𝗝𝗮𝗰𝗸𝘀𝗼𝗻 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲
Transported meth on his truck route to pay for his dying toddler's $250,000 bone marrow transplant after insurance dropped them.
𝗚𝗲𝗼𝗿𝗴𝗲 𝗠𝗮𝗿𝘁𝗼𝗿𝗮𝗻𝗼 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲
Pleaded guilty to drug charges expecting 40-54 months per the prosecution's own recommendation.
The judge gave him the maximum to pressure him into snitching on the Philly mob.
𝗧𝗶𝗺𝗼𝘁𝗵𝘆 𝗧𝘆𝗹𝗲𝗿 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲Mailed LSD to a Grateful Dead concert friend.
Two prior nonviolent drug offenses triggered the federal three-strikes provision.
𝗙𝗮𝘁𝗲 𝗪𝗶𝗻𝘀𝗹𝗼𝘄 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲
Acted as a $5 middleman in a $20 crack sale to an undercover cop in Shreveport, Louisiana.
𝗖𝗼𝗿𝘃𝗮𝗶𝗻 𝗖𝗼𝗼𝗽𝗲𝗿 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲
Federal marijuana conspiracy.
Never touched the product, no violence.
Sentenced under the federal three-strikes drug law.
𝗣𝗮𝘁𝗿𝗶𝗰𝗸 𝗠𝗮𝘁𝘁𝗵𝗲𝘄𝘀 | 𝗟𝗶𝗳𝗲 𝘄𝗶𝘁𝗵𝗼𝘂𝘁 𝗽𝗮𝗿𝗼𝗹𝗲
Stole tools from a shed in Slidell, Louisiana.
Enhanced by prior nonviolent convictions under habitual offender laws.
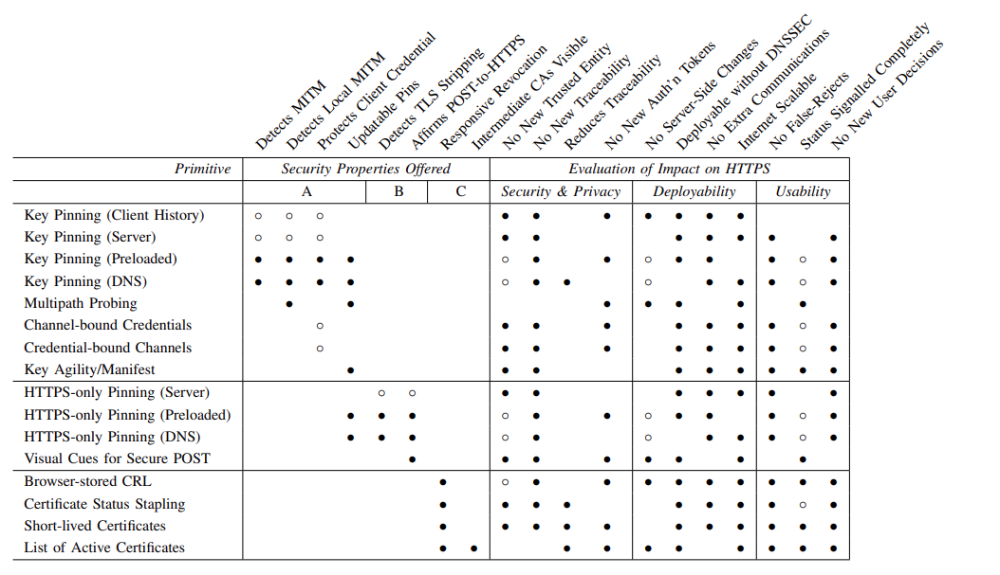
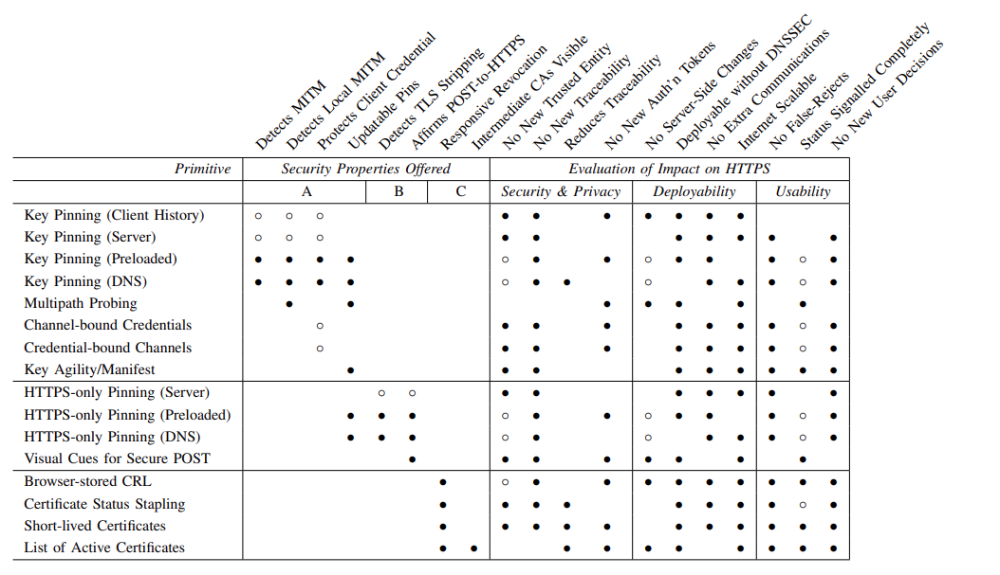
SSL/TLS ecosystem analysis showing pervasive implementation failures.
"We systematize knowledge about SSL/TLS and present a comprehensive analysis of its security."
- 𝗦𝗼𝗞: 𝗦𝗦𝗟 𝗮𝗻𝗱 𝗛𝗧𝗧𝗣𝗦: 𝗥𝗲𝘃𝗶𝘀𝗶𝘁𝗶𝗻𝗴 𝗽𝗮𝘀𝘁 𝗰𝗵𝗮𝗹𝗹𝗲𝗻𝗴𝗲𝘀 𝗮𝗻𝗱 𝗲𝘃𝗮𝗹𝘂𝗮𝘁𝗶𝗻𝗴 𝗰𝗲𝗿𝘁𝗶𝗳𝗶𝗰𝗮𝘁𝗲 𝘁𝗿𝘂𝘀𝘁 𝗺𝗼𝗱𝗲𝗹 𝗲𝗻𝗵𝗮𝗻𝗰𝗲𝗺𝗲𝗻𝘁𝘀 by Jeremy Clark and Paul C. van Oorschot (2013)
https://www.ieee-security.org/TC/SP2013/papers/4977a511.pdf
#OPSEC365 009/365
Your trash tells a story about you every week.
Prescription bottles with your name and medications, bank statements with account numbers, shipping labels with your address, and receipts that show where you shop and what you buy. Anyone willing to go through your garbage can build a detailed profile without breaking any laws.
Before your next trash day, look through what you're throwing out and see what you'd learn about yourself.
A cross-cut shredder handles paper, but don't forget about labels on packaging and prescription bottles. Peel them off, shred them, or black them out with a marker before they go in the bin. The few seconds it takes is cheaper than the identity theft it prevents.
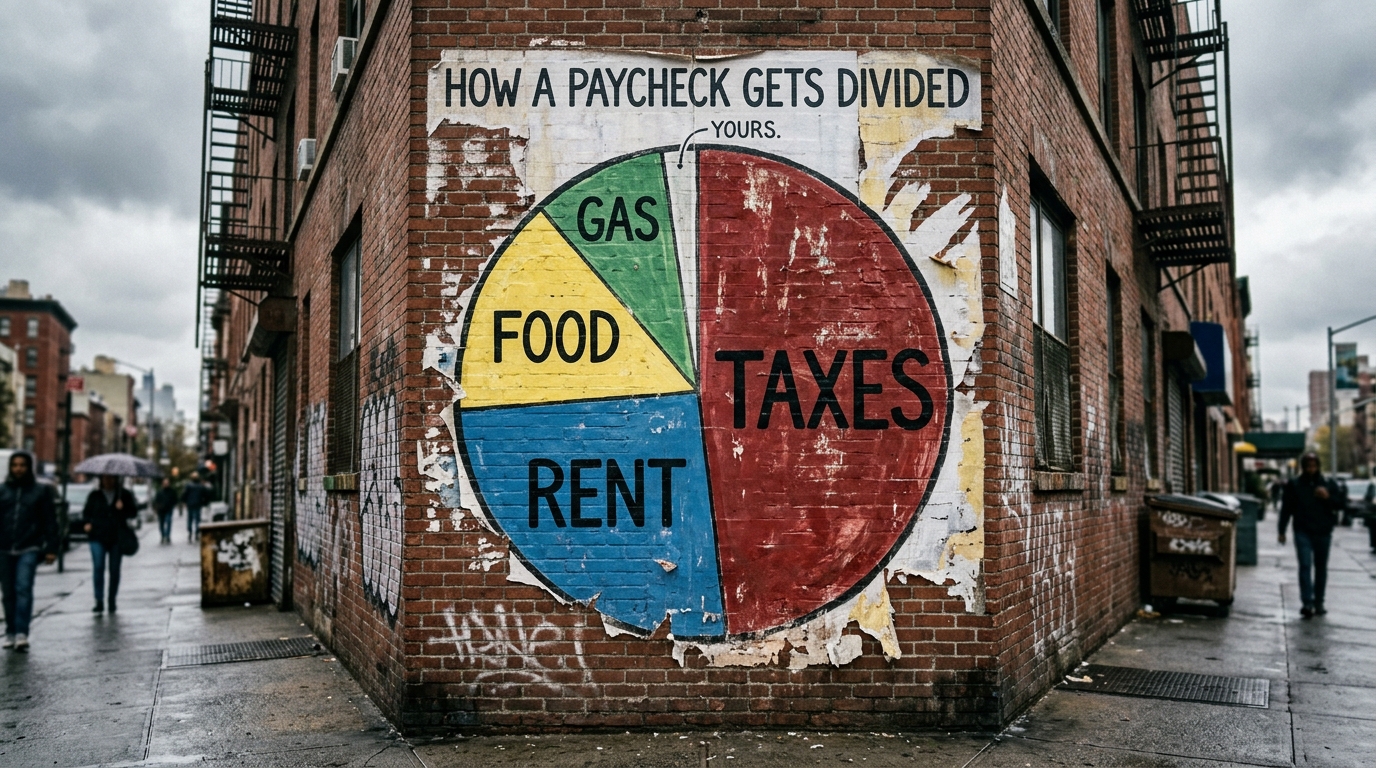
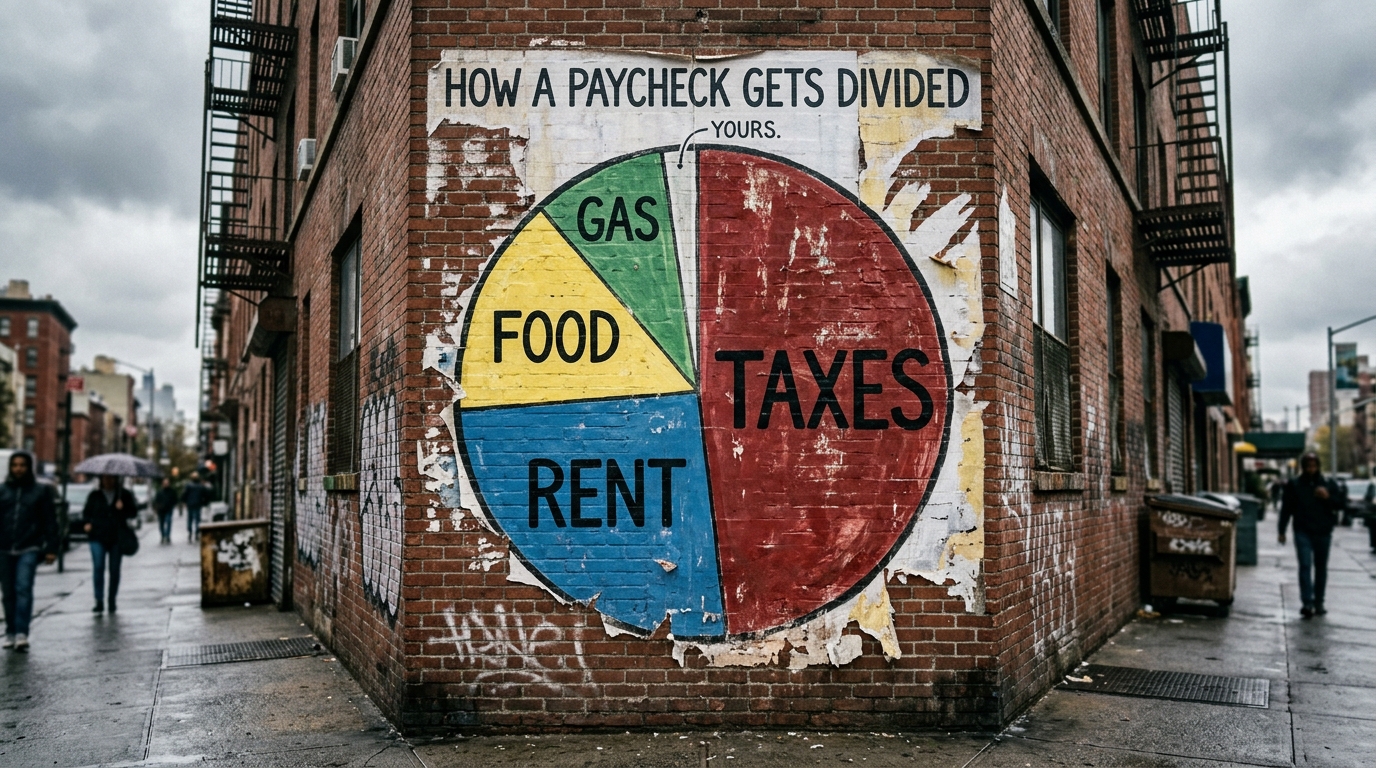
Medieval peasants kept more of their harvest than you keep of your paycheck.
#OPSEC365 008/365
Everyone has an adversary, whether they realize it or not.
It might be an ex who won't let go, a competitor digging for leverage, a scammer building a target list, or a future employer searching your name. The question isn't whether someone wants information about you, it's who and why.
Write down the three most likely people or groups who might want to know more about you than you'd want them to.
Your adversary determines your threat model, and your threat model determines what precautions make sense.
The White House app ships with a sanctioned Chinese tracking SDK,
the FBI app serves ads,
and FEMA wants 28 permissions to show you weather alerts.



Sam Bent
Fedware: 13 Government Apps That Spy Harder Than the Apps They Ban
The White House app ships with a sanctioned Chinese tracking SDK, the FBI app serves ads, and FEMA wants 28 permissions to show you weather alerts.

Monero devs have never once suggested building backdoors for law enforcement,
Zcash's founder suggested it publicly then asked you to memory-hole his own words.

