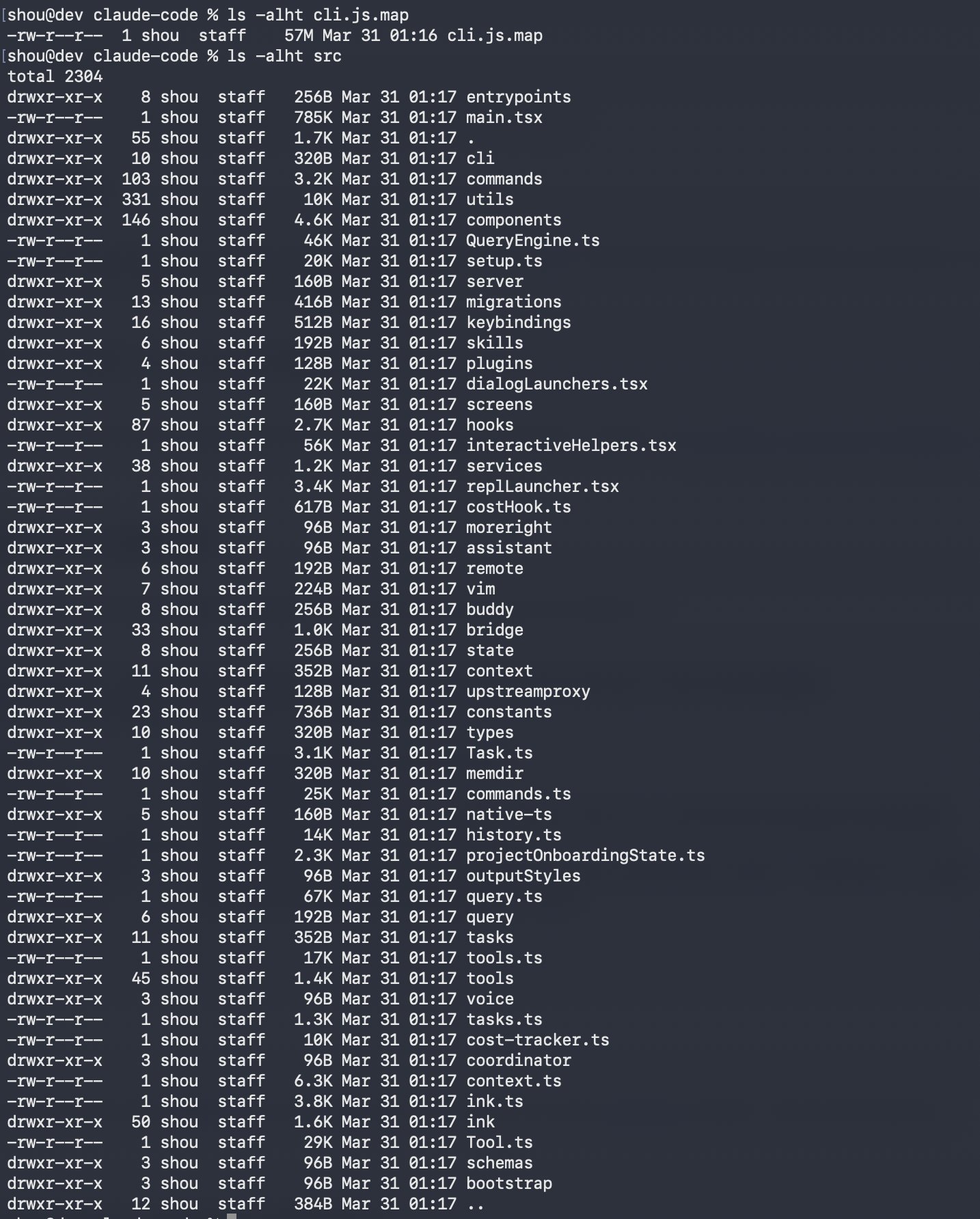
Claude code's source apparently got leaked
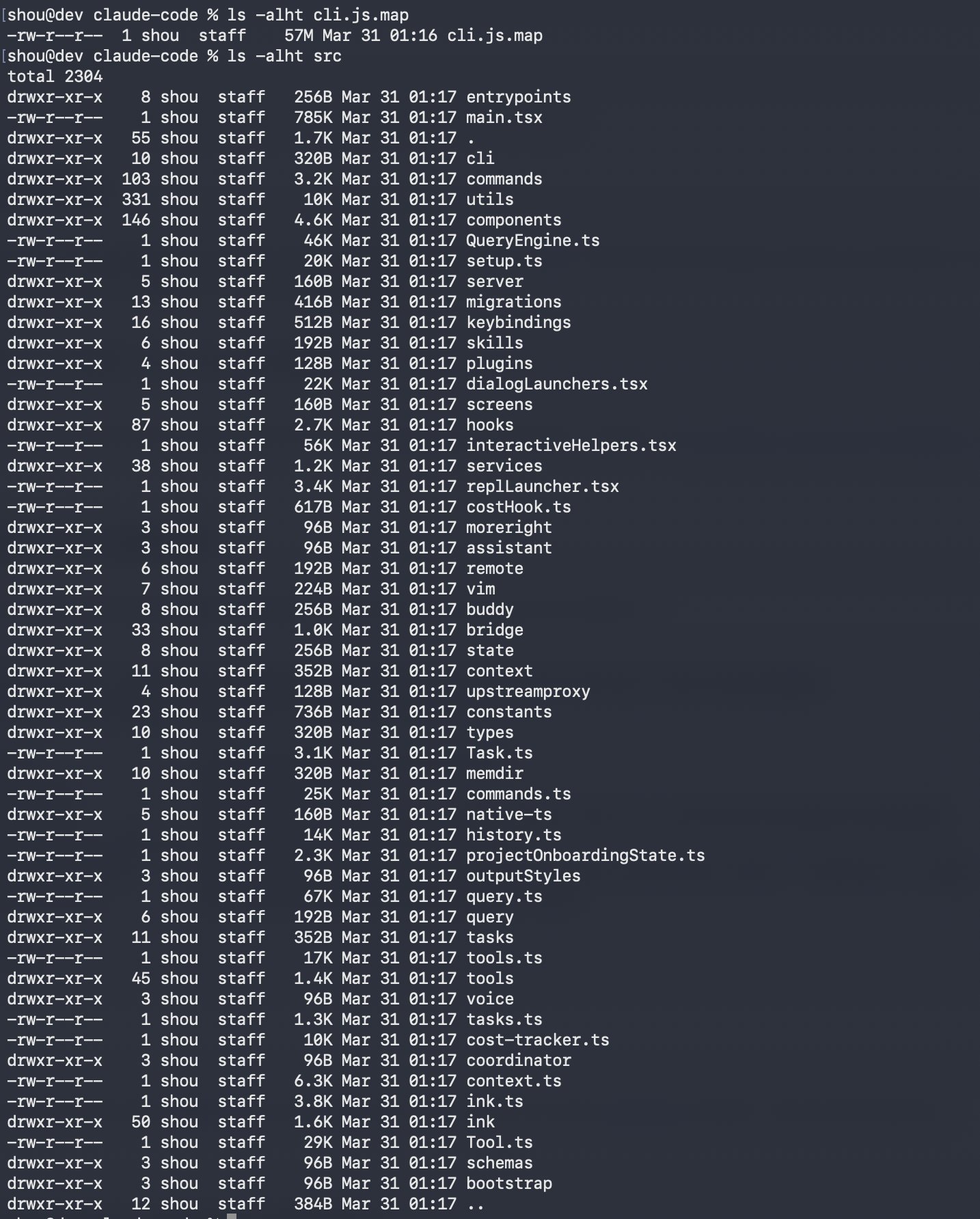 Untwittered link: https://pub-aea8527898604c1bbb12468b1581d95e.r2.dev/src.zip
Asked claude to analyse it and find data collection patterns 😂 This was the reponse
Tracking Systems Found
1. Datadog — 64 event types batched every 15s to http-intake.logs.us5.datadoghq.com with a hardcoded public API token
2. First-Party Event Logging — Rich structured events to api.anthropic.com/api/event_logging/batch with disk-backed retry (survives
crashes)
3. BigQuery Metrics — OpenTelemetry counters/histograms to api.anthropic.com/api/claude_code/metrics
4. GrowthBook — Feature flags + A/B experiment assignments with user attributes sent for targeting
5. Session Tracing (Beta) — Full OpenTelemetry distributed tracing of every user interaction, LLM call, and tool execution
Most Notable Findings
- Persistent device ID (64-char random hex) stored in ~/.claude/config.json, sent with every event
- Git repo hashing — SHA256 of your git remote URL is sent, enabling repository correlation
- Email harvested from OAuth, env vars, and git config --get user.email
- GitHub Actions CI metadata collected (actor, repo, owner IDs)
- System profiling — installed package managers, runtimes, terminal type, OS details, CPU/memory usage
- Failed telemetry persisted to disk at ~/.claude/telemetry/ and retried on next session
- Message fingerprinting — chars at positions 4, 7, 20 of your first message are hashed for attribution
How to Opt Out
export DISABLE_TELEMETRY=1 # disables analytics
export CLAUDE_CODE_DISABLE_NONESSENTIAL_TRAFFIC=1 # nuclear option
Now going to use docker to run claude. Probably should already have used it from the beginning.
#claude #privacy
Untwittered link: https://pub-aea8527898604c1bbb12468b1581d95e.r2.dev/src.zip
Asked claude to analyse it and find data collection patterns 😂 This was the reponse
Tracking Systems Found
1. Datadog — 64 event types batched every 15s to http-intake.logs.us5.datadoghq.com with a hardcoded public API token
2. First-Party Event Logging — Rich structured events to api.anthropic.com/api/event_logging/batch with disk-backed retry (survives
crashes)
3. BigQuery Metrics — OpenTelemetry counters/histograms to api.anthropic.com/api/claude_code/metrics
4. GrowthBook — Feature flags + A/B experiment assignments with user attributes sent for targeting
5. Session Tracing (Beta) — Full OpenTelemetry distributed tracing of every user interaction, LLM call, and tool execution
Most Notable Findings
- Persistent device ID (64-char random hex) stored in ~/.claude/config.json, sent with every event
- Git repo hashing — SHA256 of your git remote URL is sent, enabling repository correlation
- Email harvested from OAuth, env vars, and git config --get user.email
- GitHub Actions CI metadata collected (actor, repo, owner IDs)
- System profiling — installed package managers, runtimes, terminal type, OS details, CPU/memory usage
- Failed telemetry persisted to disk at ~/.claude/telemetry/ and retried on next session
- Message fingerprinting — chars at positions 4, 7, 20 of your first message are hashed for attribution
How to Opt Out
export DISABLE_TELEMETRY=1 # disables analytics
export CLAUDE_CODE_DISABLE_NONESSENTIAL_TRAFFIC=1 # nuclear option
Now going to use docker to run claude. Probably should already have used it from the beginning.
#claude #privacy
X (formerly Twitter)
Chaofan Shou (@Fried_rice) on X
Claude code source code has been leaked via a map file in their npm registry!
Code: https://t.co/jBiMoOzt8G
