To the "don’t trust the system" and "begging won’t help" privacy cynics: I’m one of you.
I don’t trust the state (any state!) one bit.
I live behind Tor/VPNs, I literally burn devices, no IP, no ID, no KYC, "everyone is a fed" mentality & building the parallel economy that will one day make the state irrelevant.
But some of our brothers are already inside the state's meat grinder: jailed for writing code that protects YOU.
They can’t do anything anymore.
They can only stare at a signature counter and hope.
You know that little dopamine hit when the notification bell goes +1… of course you know - you see this msg on some social network ;)
For them, every new signature is that bell.
Except theirs decides whether they walk free or rot in a cage.
You don’t have to "believe in the system".
Just give them one more red notification, one more dopamine hit, one more spark of hope.
If your heart is too armored for empathy, borrow mine.
Fight on both fronts... anonymously/pseudonymously.
#FreeSamourai
https://www.change.org/p/stand-up-for-freedom-pardon-the-innocent-coders-jailed-for-building-privacy-tools

AilliA
AilliA@aillia.link
npub1ajll...d9u3
I believe that anything that is not voluntary is coercion.
This makes me a voluntaryist in earthly terms and an alien on Earth, where coercion is normalized. #Monero: 86VSR7QowFkiqxsvZrW9w6B1WLtCBpQEgjFVWW1sCyHE14ivHXfZoAeQWpGn5EKbcs4Z3sV5T2Vfie5bY5pSykg97vJXpRA
PSA #XmrBazaar: Active fake/wrapped token scam in the Exchange category
A user (BigWhale1) is trying to scam people by “sending” BEP-20 LTC on the BNB Smart Chain.
The transaction is real and will show up on BSCScan with your correct wallet address
Example TX:  What looks like “5.27 LTC” being sent to you is actually a completely fake token.
How to spot it instantly:
- Click the token name “LTC” in the transaction details
- You’ll be taken to the fake contract: 0xacdb…2dfe
- Real Binance-Peg Litecoin lives at: 0x4338665CBB7B2485A8858A139b75D5e34AB3DB94
- The fake one has almost no holders, no liquidity, and $0 value
This is a classic dusting/impersonation scam!
You didn’t receive any real LTC: nothing of value was sent!!!
Stay safe and always double-check the contract address!
What looks like “5.27 LTC” being sent to you is actually a completely fake token.
How to spot it instantly:
- Click the token name “LTC” in the transaction details
- You’ll be taken to the fake contract: 0xacdb…2dfe
- Real Binance-Peg Litecoin lives at: 0x4338665CBB7B2485A8858A139b75D5e34AB3DB94
- The fake one has almost no holders, no liquidity, and $0 value
This is a classic dusting/impersonation scam!
You didn’t receive any real LTC: nothing of value was sent!!!
Stay safe and always double-check the contract address!


BNB Smart Chain Explorer
Bsc Transaction Hash: 0x409737e986... | BscScan
Transfer 5.27 LTC to 0x5F6c330C...624357eD5 | Success | Nov-20-2025 10:49:30 AM (UTC)

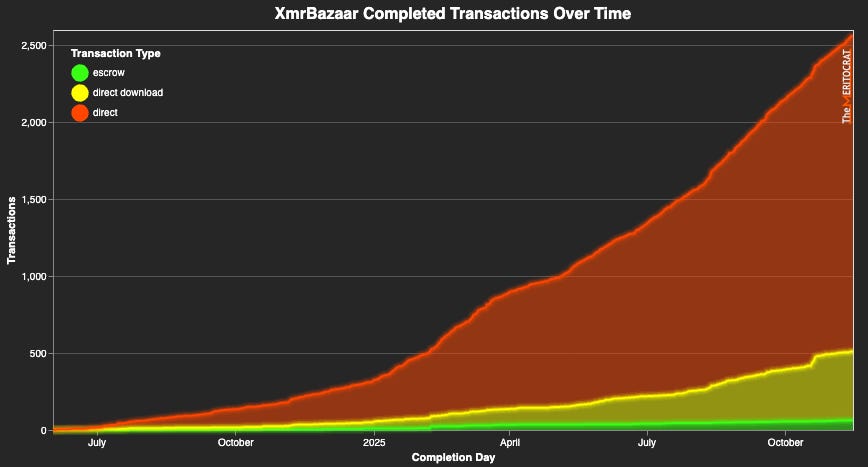
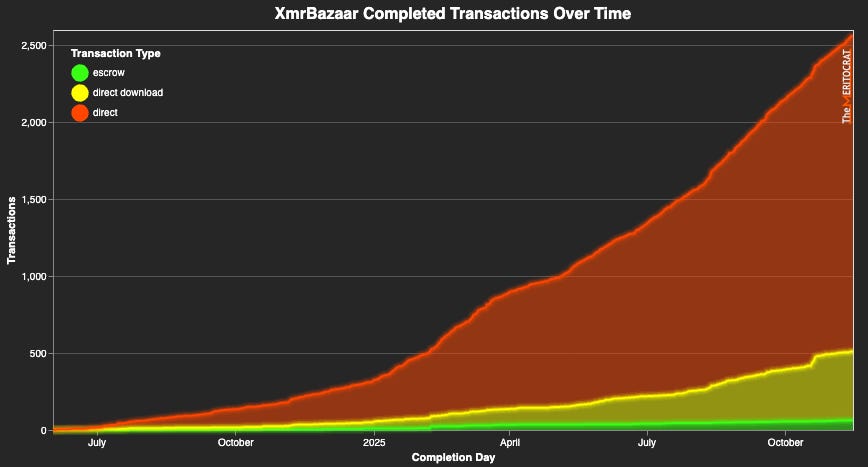
XmrBazaar - Monero Marketplace
Buy and sell products and services for Monero
It would mean a lot if you would sign this petition calling on Donald Trump to pardon Keonne and Bill
https://www.change.org/p/stand-up-for-freedom-pardon-the-innocent-coders-jailed-for-building-privacy-tools
In 30 days they will report to prison. Unless the President steps in.
Developers shouldn't be liable for the actions of bad actors using their software
#freesamourai



X (formerly Twitter)
Keonne Rodriguez (@keonne) on X
It would mean a lot if you would sign this petition calling on @realDonaldTrump to pardon me and Bill
In 30 days we will report to prison. Unless...

"The internet is a bad idea." - Newspapers
"Uber is a bad idea." - Taxis
"Airbnb is a bad idea." - Hotels
"Monero is a bad idea." - States
"Freedom is a bad idea." - NPCs
"A bank or other financial service provider will be able to immediately freeze or suspend an account without a court order"

X (formerly Twitter)
Russell Brand (@rustyrockets) on X
"A bank or other financial service provider will be able to immediately freeze or suspend an account without a court order"

#FreeSamourai


List of Bonded #Monero Traders.
Live & constantly updated (whenever bonds are added, renewed, or expire).


List of Bonded Monero Traders
Last update: 2026-03-03. Live & constantly updated (whenever bonds are added, renewed, or expire).
What an XmrBazaar #Monero Multisig Escrow Mediator Actually Is (and What It Is NOT)
Notes on Personal Responsibility, #XmrBazaar Green Trust Levels, Escrow, and Bonds


What an XmrBazaar Monero Multisig Escrow Mediator Actually Is (and What It Is NOT)
Notes on Personal Responsibility, XmrBazaar Green Trust Levels, Escrow, and Bonds
Now it gets too ridiculous: https://x.com/AilliaLink account is fully suspended again (after they themselves restored it after review!) for "inauthentic behavior": and this time it was an already restricted account that she wasn't even able to use to "behave" AT ALL!
Apparently, doing nothing because your account is restricted (and you can't really do anything!!!) is also considered 'inauthentic behavior'...


Frogs cannot sense a slow change in the temp of the water around them. If you plunge them into boiling water they'll immediately jump out. But if you place them into room temperature water and slowly heat it to boiling, the frog won't notice and will slowly cook to death.
The End.
https://x.com/realUrbanHacker/status/1988882930249203980






Institutionalized people like Balaji allowed KYC to happen in the first place. Now they're talking "privacy" with ZKYC... (https://x.com/balajis/status/1988875262700781792)
...and in all his ~31K tweets, he has mentioned Monero 3 times:
https://x.com/search?q=Monero%20from%3Abalajis


Congratulations @Soul Reaver, winner of the 0.25 Monero hidden inside my Steganography 101: Hiding Wallet Seeds in Plain Sight article! 🏆
It was such a fun burst of impromptu thinking on my part: While writing (VTT-ing) a reply to that XMRChat question about @The Watchman Privacy Podcast 's Cards, I wondered: what might a pinprick analogue look like in this (rather limited!) Substack editor? Then, as I was writing about foreign/ancient languages, I remembered homoglyphs... it was a fun moment!
So I tossed words with homoglyphs in reverse order into the article, because I knew it'd otherwise be a zero-shot giveaway for AI (that's exactly how I double-checked myself to ensure I hadn't missed a single word 😜 ).
 View quoted note →
View quoted note →
 View quoted note →
View quoted note →Steganography 101: Hiding #Monero Wallet Seeds in Plain Sight
0.25 XMR Hidden Inside: An Improv Puzzle Response to an XMRChat Query on @The Watchman Privacy Podcast 's Greeting Card Method


Steganography 101: Hiding Wallet Seeds in Plain Sight
0.25 XMR Hidden Inside: An Improv Puzzle Response to an XMRChat Query on Watchman Privacy's Greeting Card Method
🖼️ #XmrBazaar Banner Design Competition
Be the Artist, the Judge, or the Voice in Our Competition: Pure Free-Market #Monero-Style Meritocracy
Submissions open now!
Read more 👇



XmrBazaar Banner Design Competition
Hey XmrBazaar fans and our beloved Monero Matrix and X critics!

I am in crypto for this. 

You really should read the cypherpunk manifesto.
A Cypherpunk's Manifesto
by Eric Hughes
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world.
If two parties have some sort of dealings, then each has a memory of their interaction. Each party can speak about their own memory of this; how could anyone prevent it? One could pass laws against it, but the freedom of speech, even more than privacy, is fundamental to an open society; we seek not to restrict any speech at all. If many parties speak together in the same forum, each can speak to all the others and aggregate together knowledge about individuals and other parties. The power of electronic communications has enabled such group speech, and it will not go away merely because we might want it to.
Since we desire privacy, we must ensure that each party to a transaction have knowledge only of that which is directly necessary for that transaction. Since any information can be spoken of, we must ensure that we reveal as little as possible. In most cases personal identity is not salient. When I purchase a magazine at a store and hand cash to the clerk, there is no need to know who I am. When I ask my electronic mail provider to send and receive messages, my provider need not know to whom I am speaking or what I am saying or what others are saying to me; my provider only need know how to get the message there and how much I owe them in fees. When my identity is revealed by the underlying mechanism of the transaction, I have no privacy. I cannot here selectively reveal myself; I must always reveal myself.
Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy.
Privacy in an open society also requires cryptography. If I say something, I want it heard only by those for whom I intend it. If the content of my speech is available to the world, I have no privacy. To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy. Furthermore, to reveal one's identity with assurance when the default is anonymity requires the cryptographic signature.
We cannot expect governments, corporations, or other large, faceless organizations to grant us privacy out of their beneficence. It is to their advantage to speak of us, and we should expect that they will speak. To try to prevent their speech is to fight against the realities of information. Information does not just want to be free, it longs to be free. Information expands to fill the available storage space. Information is Rumor's younger, stronger cousin; Information is fleeter of foot, has more eyes, knows more, and understands less than Rumor.
We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.
We the Cypherpunks are dedicated to building anonymous systems. We are defending our privacy with cryptography, with anonymous mail forwarding systems, with digital signatures, and with electronic money.
Cypherpunks write code. We know that someone has to write software to defend privacy, and since we can't get privacy unless we all do, we're going to write it. We publish our code so that our fellow Cypherpunks may practice and play with it. Our code is free for all to use, worldwide. We don't much care if you don't approve of the software we write. We know that software can't be destroyed and that a widely dispersed system can't be shut down.
Cypherpunks deplore regulations on cryptography, for encryption is fundamentally a private act. The act of encryption, in fact, removes information from the public realm. Even laws against cryptography reach only so far as a nation's border and the arm of its violence. Cryptography will ineluctably spread over the whole globe, and with it the anonymous transactions systems that it makes possible.
For privacy to be widespread it must be part of a social contract. People must come and together deploy these systems for the common good. Privacy only extends so far as the cooperation of one's fellows in society. We the Cypherpunks seek your questions and your concerns and hope we may engage you so that we do not deceive ourselves. We will not, however, be moved out of our course because some may disagree with our goals.
The Cypherpunks are actively engaged in making the networks safer for privacy. Let us proceed together apace.
Onward.
Eric Hughes <hughes@soda.berkeley.edu>
9 March 1993

A Cypherpunk's Manifesto

You build atomic bombs, you wage wars, you murder, cheat, and lie to us and try to make us believe it's for our own good, yet we're the criminals.


Phrack
Hacker
Click to read the article on phrack



