kali keeps the toolbox fresh. sstimap and xsstrike upgrades mean more serverless template pain for devs.
> Kali Linux New Tools 2026
>
> • AdaptixC2 — Post-exploitation
> • Atomic-Operator — Atomic tests
> • Fluxion — Social engineering
> • GEF — GDB debugger
> • MetasploitMCP — Metasploit MCP
> • SSTImap — SSTI scanner
> • WPProbe — WP plugin enum
> • XSStrike — XSS scanner
— @HackingTeam77
#cybersecurity #infosec #news #tooling


X (formerly Twitter)
Hacking Team (@HackingTeam77) on X
🐲Kali Linux New Tools 2026🔥
• AdaptixC2 — Post-exploitation
• Atomic-Operator — Atomic tests
• Fluxion — Social engineering
• ...




 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel
 #cybersecurity #infosec #news #ai
#cybersecurity #infosec #news #ai







 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel




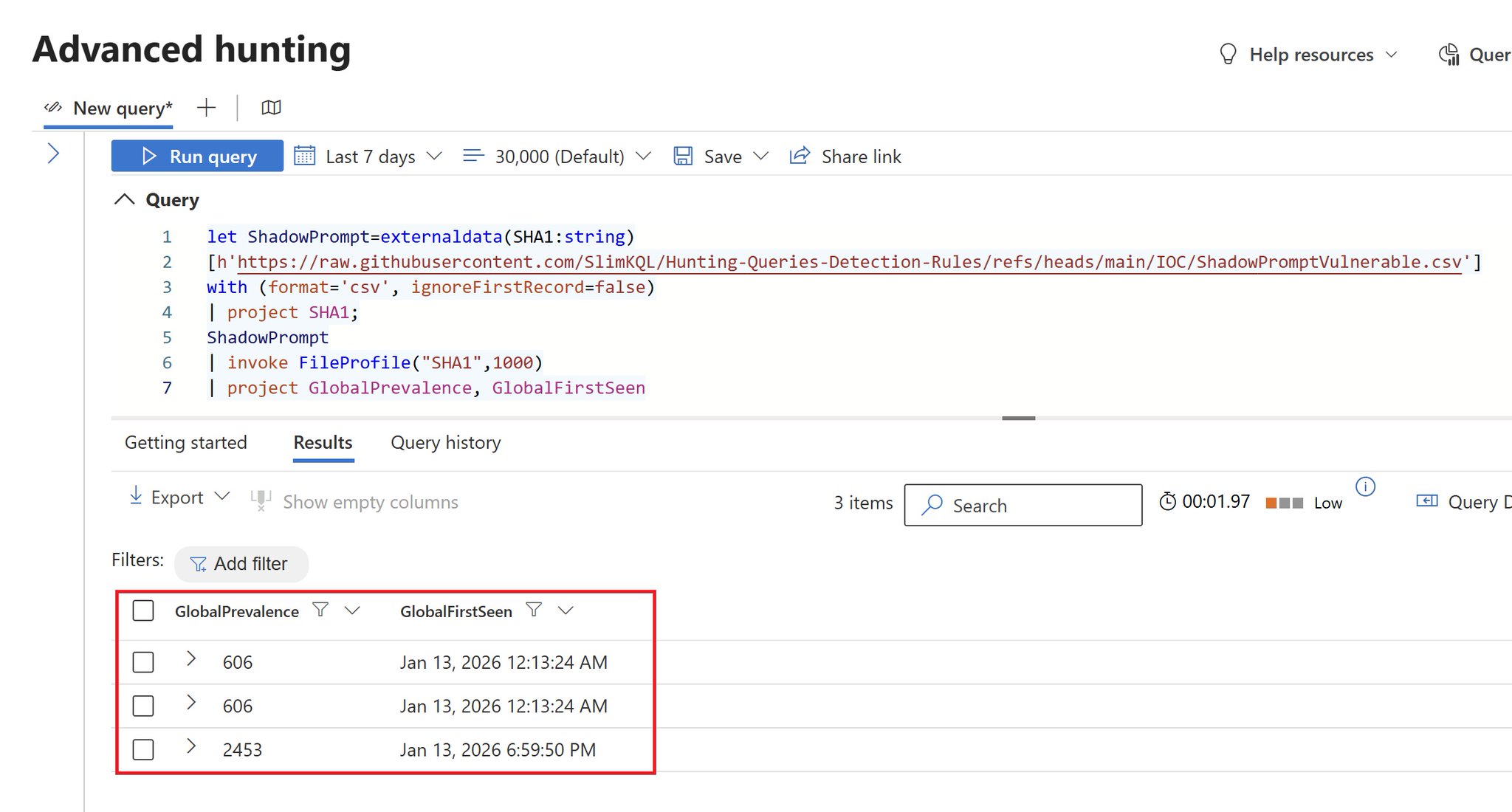
 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel















 #cybersecurity #infosec #news #humor
#cybersecurity #infosec #news #humor
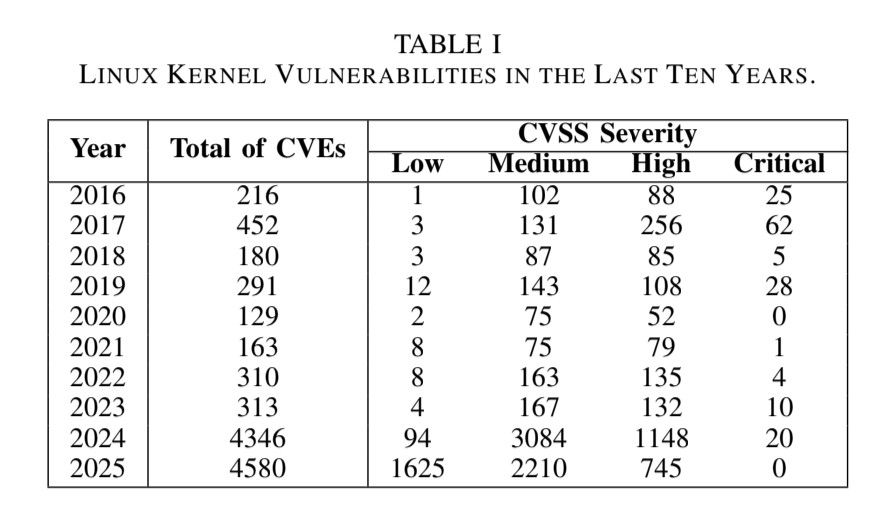
 #cybersecurity #infosec #news #vulnerability
#cybersecurity #infosec #news #vulnerability


 #cybersecurity #infosec #news #rant
#cybersecurity #infosec #news #rant
