> JD Vance: "the US government does not even prosecute fraud if it is under $1.5M per year"
>
> Literally every criminal on the planet:
— @vxunderground
 #cybersecurity #infosec #news #rant
#cybersecurity #infosec #news #rant

 #cybersecurity #infosec #news #rant
#cybersecurity #infosec #news #rant

X (formerly Twitter)
vx-underground (@vxunderground) on X
JD Vance: "the US government does not even prosecute fraud if it is under $1.5M per year"
Literally every criminal on the planet:

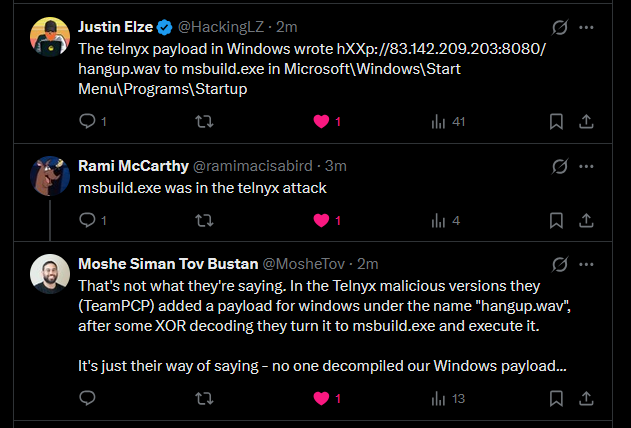
 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel




 #cybersecurity #infosec #news #humor
#cybersecurity #infosec #news #humor

 #cybersecurity #infosec #news #tooling
#cybersecurity #infosec #news #tooling

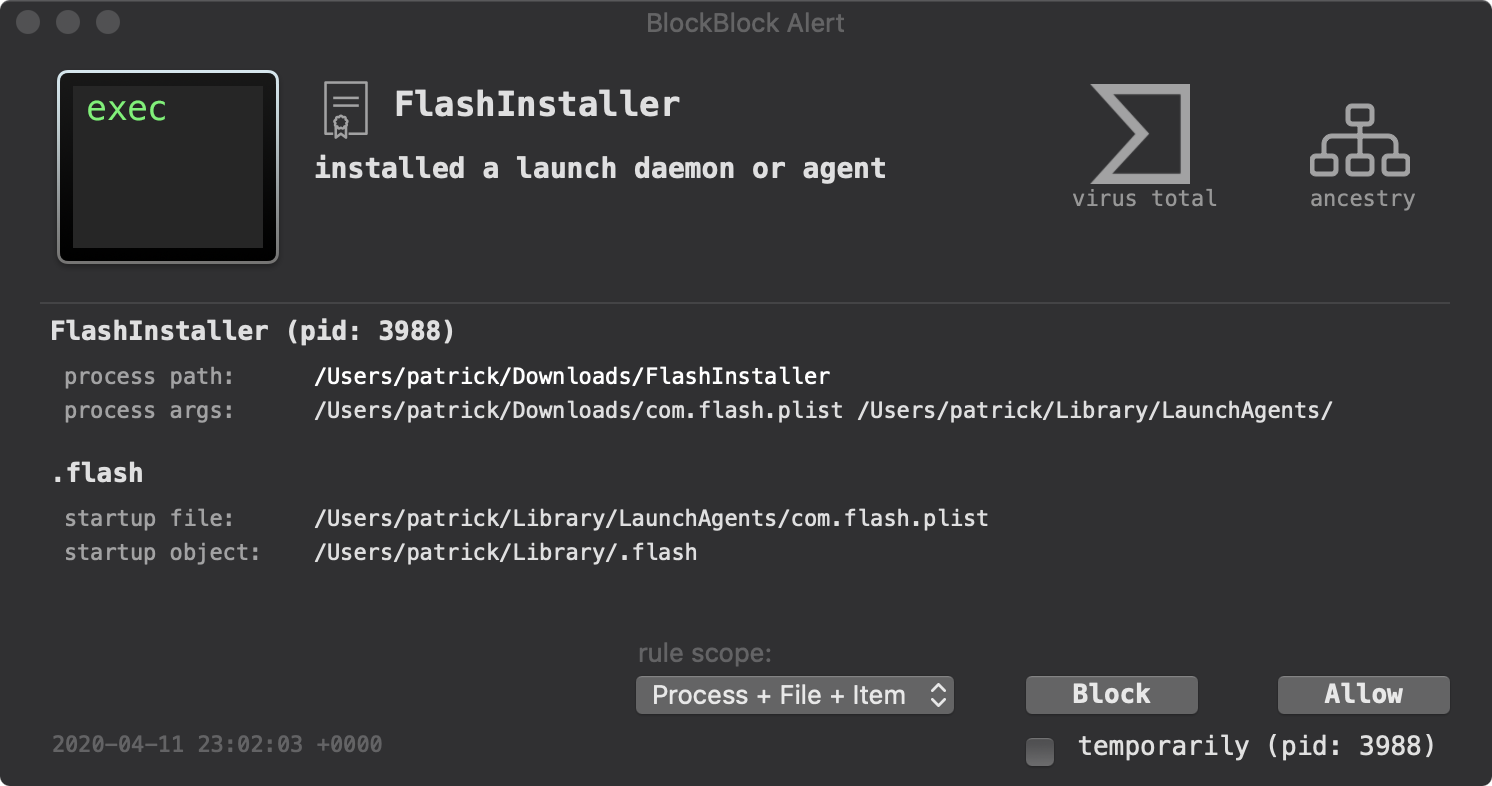
 #cybersecurity #infosec #news #tooling
#cybersecurity #infosec #news #tooling








 #cybersecurity #infosec #news #rant
#cybersecurity #infosec #news #rant









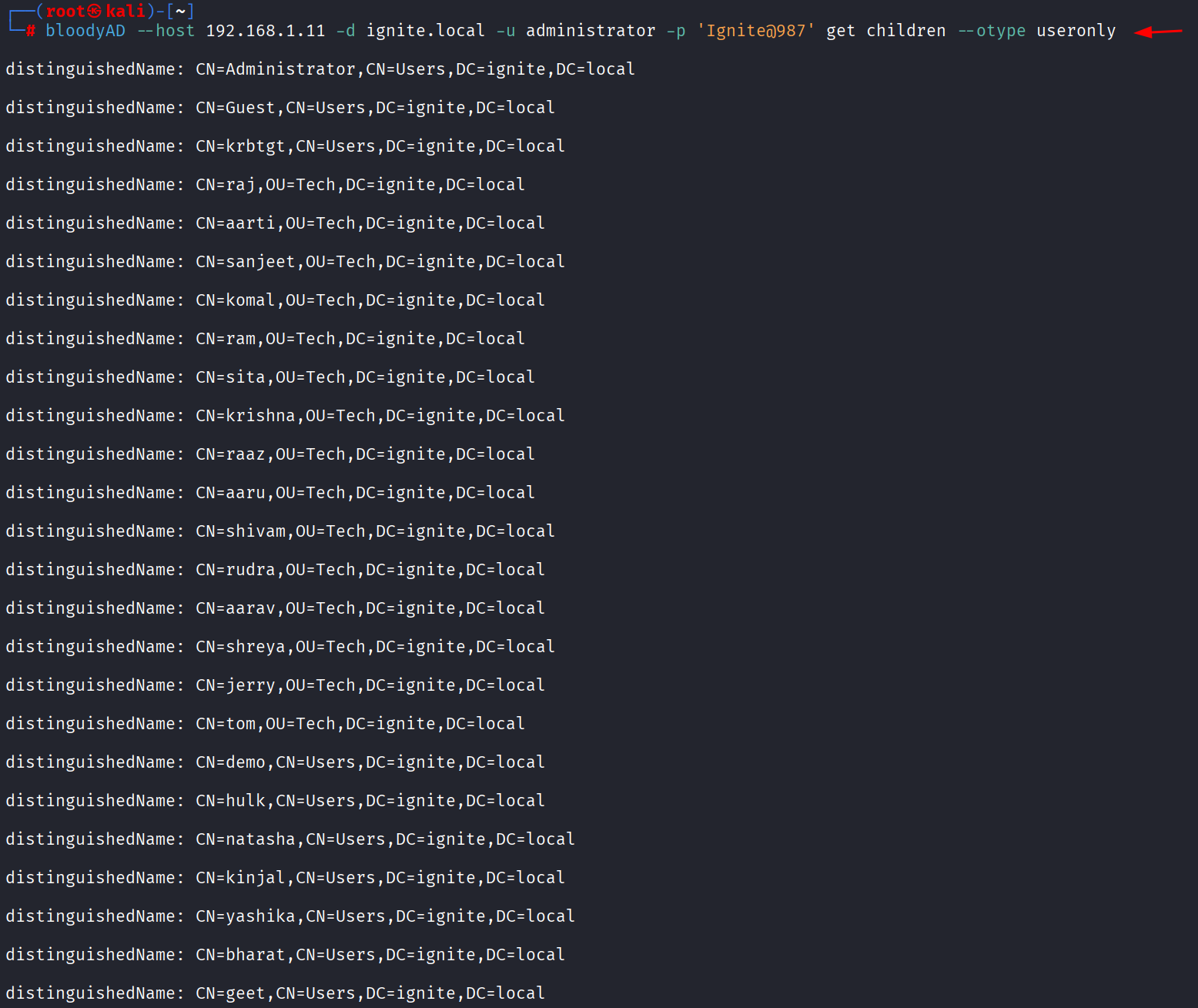
 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel




 #cybersecurity #infosec #news #research
#cybersecurity #infosec #news #research
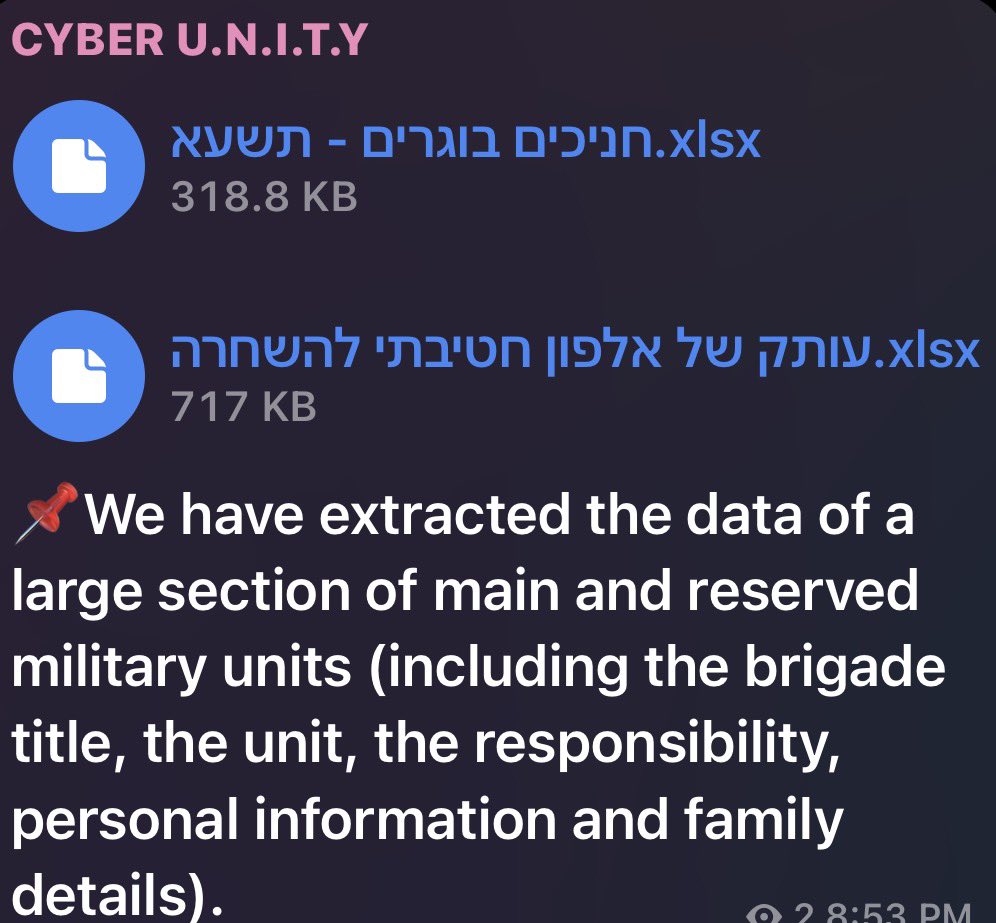
 #cybersecurity #infosec #news #threat-intel
#cybersecurity #infosec #news #threat-intel
 #cybersecurity #infosec #news #digitalid
#cybersecurity #infosec #news #digitalid

