anthropic cooking up an ai strong in cybersecurity. deliberate release means they're scared of what it can break.
> Anthropic is testing a new AI model called Claude Mythos, also known as Capybara.
>
> “We’re developing a general purpose model with meaningful advances in reasoning, coding, and cybersecurity.
>
> Given the strength of its capabilities, we’re being deliberate about how we release it.
— @Pirat_Nation

 #cybersecurity #infosec #news #ai
#cybersecurity #infosec #news #ai




X (formerly Twitter)
Pirat_Nation 🔴 (@Pirat_Nation) on X
Anthropic is testing a new AI model called Claude Mythos, also known as Capybara.
“We’re developing a general purpose model with meaningful ad...



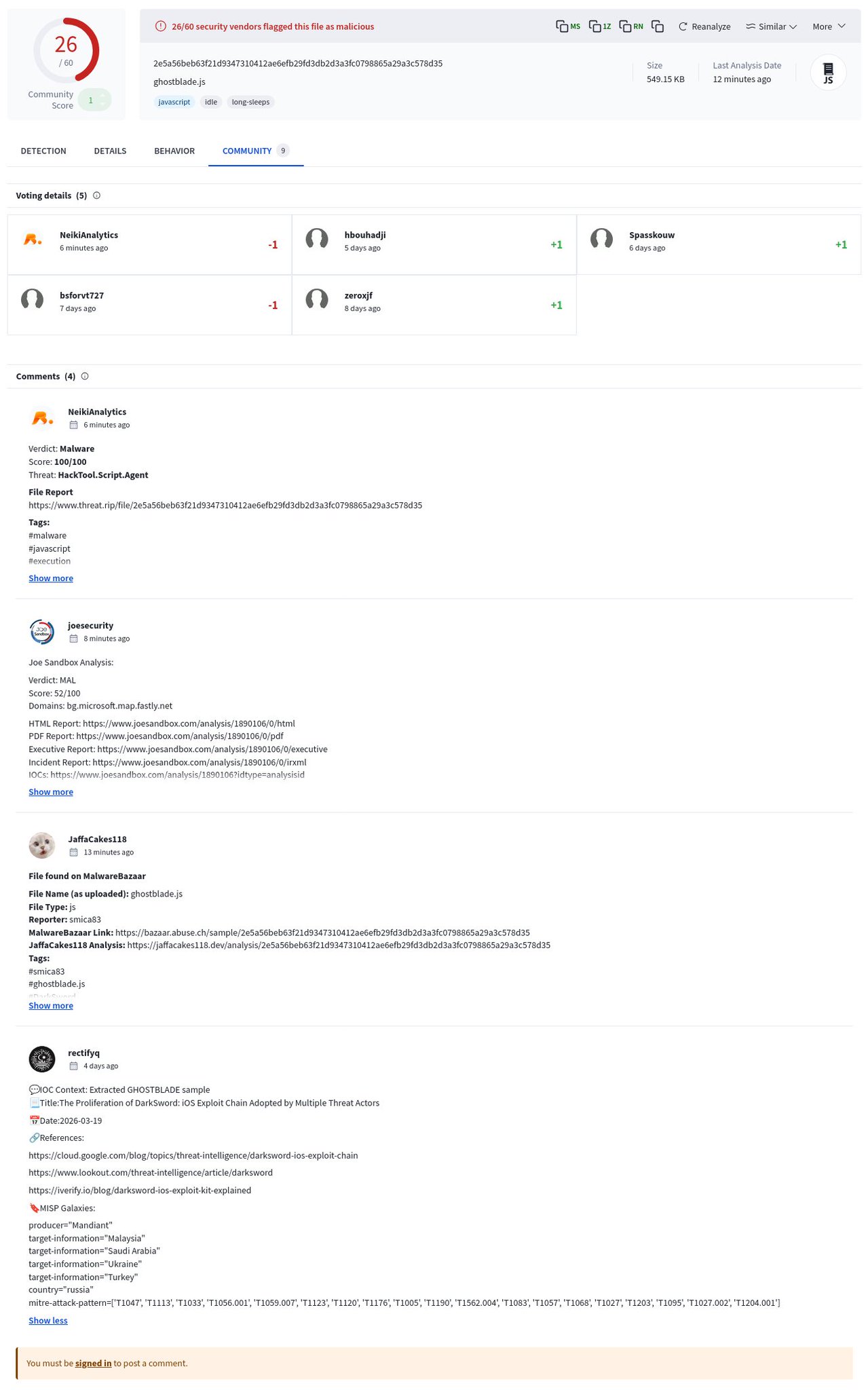
 #cybersecurity #infosec #news #humor
#cybersecurity #infosec #news #humor




 #cybersecurity #infosec #news #humor
#cybersecurity #infosec #news #humor










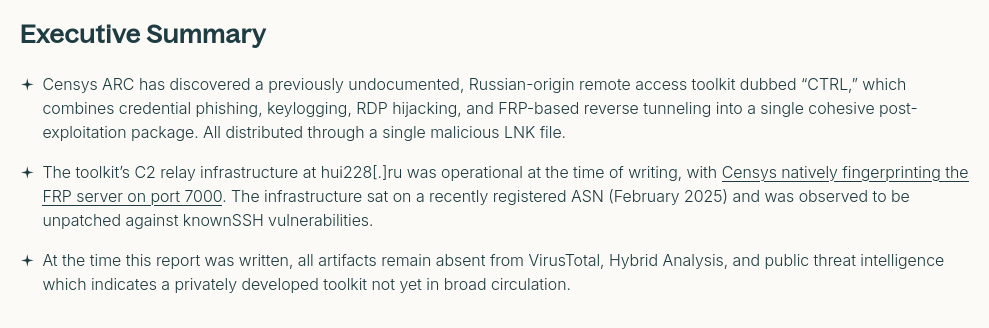
 #cybersecurity #infosec #news #incident
#cybersecurity #infosec #news #incident









 #cybersecurity #infosec #incident
#cybersecurity #infosec #incident