The woke media attacks Trump so much about total bullshit, that people learn to ignore any real criticism as well. And that's where the real danger is
SimplifiedPrivacy.com
npub14slk...t5d6
Give me Liberty, or Give me Death. HydraVeil is our Revolutionary New Linux app that allows you to create different isolated profiles, to resist AI Browser Fingerprinting from Cloudflare & Big Tech. Another feature of HydraVeil is routing your traffic though your choice of WireGuard or a Tor->Socks5 proxy (to evade Tor blocks), and to fool CDN packet speed tracing with different IPs for each profile.
Additionally, we provide VPN service for Android, iPhone, Windows, Mac, and Routers. Tune in to our Podcast to combat Big Tech surveillance. Help me, help you.
Hashtags: #Cypherpunk, Open source, #Linux, DeGoogled Phones, self-hosted services, #Monero, #Security, and more!
New Podcast:
Monero 101: Where to get it
 Not only will this podcast entertain and educate you, but you'll also learn about the Paradox of Monero.
What if I told you that by making restrictions, it actually cripples the ability to regulate it by under their own legal systems?
Web:
RSS:
Not only will this podcast entertain and educate you, but you'll also learn about the Paradox of Monero.
What if I told you that by making restrictions, it actually cripples the ability to regulate it by under their own legal systems?
Web:
RSS:
 Not only will this podcast entertain and educate you, but you'll also learn about the Paradox of Monero.
What if I told you that by making restrictions, it actually cripples the ability to regulate it by under their own legal systems?
Web:
Not only will this podcast entertain and educate you, but you'll also learn about the Paradox of Monero.
What if I told you that by making restrictions, it actually cripples the ability to regulate it by under their own legal systems?
Web: Monero 101: Where to get it | Simplified Privacy Podcast
Where do you get Monero? What should you avoid? Shownotes on Nostr: (remove the spaces) https://primal.net/e/ nevent1qqs9sn80yju9jt9gy9762w93xhc8 9...
Simplified Privacy Podcast
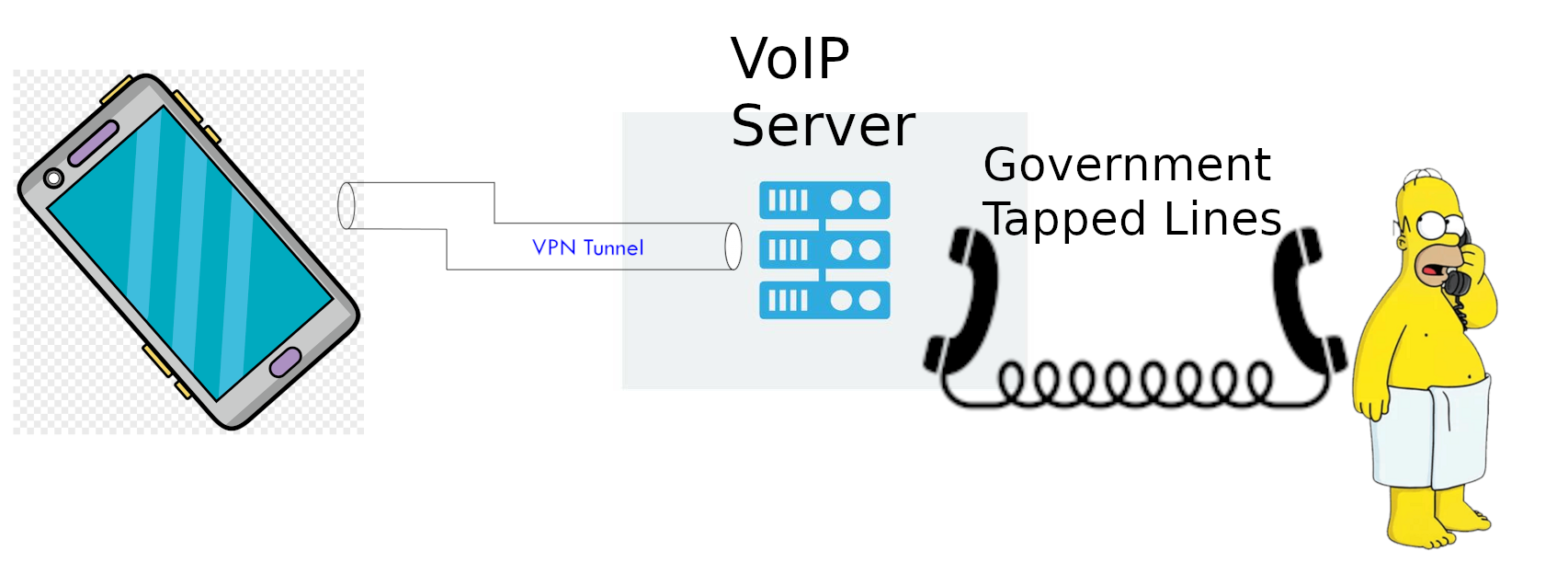 VoIP: Hides from the phone company the LOCATION of the texter, but NOT the content.
VPN: Hides from the VoIP provider your home IP, but NOT the SMS content
Hotspots (& Faraday bags): Hide from the celltower giving you service, where you go when it's bagged.
If you only use the hotspot outside the faraday bag, when you're outside your home,
And only use SMS with VoIP and a VPN, then you're as anonymous as SMS can be. But even better, is reduce/stop using SMS.
VoIP: Hides from the phone company the LOCATION of the texter, but NOT the content.
VPN: Hides from the VoIP provider your home IP, but NOT the SMS content
Hotspots (& Faraday bags): Hide from the celltower giving you service, where you go when it's bagged.
If you only use the hotspot outside the faraday bag, when you're outside your home,
And only use SMS with VoIP and a VPN, then you're as anonymous as SMS can be. But even better, is reduce/stop using SMS.US Immigration searched a French Scientist's phone, and found criticism of Donald Trump.
So they rejected him from entry at the airport/border, and labeled his private messages terrorism!
Why are they even searching people's phones at the border? Your legal entry should be based on a passport, and NOT on your social media or private messages!
Sources:
 https://www.nytimes.com/2025/03/20/world/europe/us-france-scientist-entry-trump-messages.html
https://www.nytimes.com/2025/03/20/world/europe/us-france-scientist-entry-trump-messages.html

The Independent
French scientist denied entry to US after ‘hateful’ Trump texts found on phone
The French government has defended the researcher’s ‘freedom of expression’
The only purpose in political talk, is to get you to take action
I'm NOT just saying "yo download my cool new app".
I am saying: The entire structure of our society is corrupt. From people's wealth being tracked, to surveillance of their intimate conversations with their family. And the dark history of how this came to be, unfolds in this podcast linked below.
The goal here is to not just entertain you, with this wild story of how the intelligence agencies literally did terrorism on US Congress members to get the Patriot Act passed... But to get action: transitioning to Linux, to Degoogled phones, to cryptocurrency, as the path forward. And then our team's fingerprint app can build upon this solid foundation.
In this critical context, you absolutely should check out this 10-minute podcast on the history of KYC laws:
Web:
RSS:
Subverted History! The Shocking Story of KYC Surveillance | Simplified Privacy Podcast
KYC Laws are way more corrupt than you thought. Here's how to handle them. Resources: https://www.ae911truth.org/ and Graeme MacQueen: The 2001 A...
Simplified Privacy Podcast
Subverted History!
The Shocking Story of KYC Surveillance
 What if I told you that the history of how KYC laws came to the US, was even more corrupt than the laws themselves?
In this short but sweet 10-minute podcast, Shadow Rebel breaks down the dark history of physically threatening Congress members to convince them to pass this... and worse:
Web:
RSS:
Arweave (optional)
Germany: https://shadow.arweave.auduge.com/
New York: https://shadow.exodusdiablo.xyz/
China:
What if I told you that the history of how KYC laws came to the US, was even more corrupt than the laws themselves?
In this short but sweet 10-minute podcast, Shadow Rebel breaks down the dark history of physically threatening Congress members to convince them to pass this... and worse:
Web:
RSS:
Arweave (optional)
Germany: https://shadow.arweave.auduge.com/
New York: https://shadow.exodusdiablo.xyz/
China:
 What if I told you that the history of how KYC laws came to the US, was even more corrupt than the laws themselves?
In this short but sweet 10-minute podcast, Shadow Rebel breaks down the dark history of physically threatening Congress members to convince them to pass this... and worse:
Web:
What if I told you that the history of how KYC laws came to the US, was even more corrupt than the laws themselves?
In this short but sweet 10-minute podcast, Shadow Rebel breaks down the dark history of physically threatening Congress members to convince them to pass this... and worse:
Web: Subverted History! The Shocking Story of KYC Surveillance | Simplified Privacy Podcast
KYC Laws are way more corrupt than you thought. Here's how to handle them. Resources: https://www.ae911truth.org/ and Graeme MacQueen: The 2001 A...
Simplified Privacy Podcast
Simplified Privacy Videos on Arweave
It’s extremely difficult for the average person to get the technical knowledge required for privacy, censorship resistance, and independence from Big Tech. We are here to make your life easy.
Switching to Linux:
How VoIP works:
What are the best VoIP burner SMS providers?
How Monero Works (animated)
https://video.simplifiedprivacy.com/how-xmr-works/
How GrapheneOS Works (animated)
https://video.simplifiedprivacy.com/why-grapheneos-is-more-secure/
Is Email private? What data can be gotten?
What are some great VPS anon-crypto hosts?
Why is LinkedIn evil?
Why is Google Totalitarian?
The difference between a company, and an organization, is promoting our mission. This means using all of the tools available.
Linux n00bs 101: Critical Podcast | Simplified Privacy
VoIP 101: Hiding your location | Simplified Privacy
Pro-Con of “Privacy” Phone Numbers-Services | Simplified Privacy
Is Email Private? Easy Basics | Simplified Privacy
Pro/Con of Anonymous VPS Hosts | Simplified Privacy
Linked-In Tyranny Agenda | Simplified Privacy
Google is Totalitarian | Simplified Privacy
I personally don't trust hardware wallets.
Especially if it's closed source. If you got a large enough amount of cryptocurrency to justify a hardware wallet, then I'd:
a) Split it up into a hot wallet for daily stuff, and a large cold wallet with the rest
b) Cold wallet could be KeePass inside VeraCrypt Drives, with a fake password for a hidden drive
c) With an epic amount of cryptocurrency, (this is not the vast majority of the readers), using a virtual machine, with the crypto wallets on the host, and the purchases inside the VM.
d) With a medium amount of cryptocurrency, our fingerprint app also gives you the added benefit of GUI isolation for Linux Distros like Mint, which don't have it for x11 displays. In other words, the web browser isn't seeing your keepass and wallets.