FBI extracted deleted Signal messages, even after the app was uninstalled.
When Signal messages arrive, iOS stores push notification previews locally on the device. In this case, those previews stayed behind even after Signal was uninstalled.
- Only incoming messages were captured this way
- Disappearing messages that had already vanished inside Signal were still recoverable from the notification cache
-This is iOS behavior, not a Signal vulnerability. And likely impacts other ALL apps on iOS.
The quick fix, to turn it off:
Signal → Settings → Notifications → Show → set to "No Name or Content"
You'll still get a notification ping, but iOS just won't cache anything useful.
The real fix:
Switch to GrapheneOS
The original 404media source is paywalled,
https://cybernews.com/security/fbi-extracts-signal-messages-from-suspect/


404 Media
FBI Extracts Suspect’s Deleted Signal Messages Saved in iPhone Notification Database
The case was the first time authorities charged people for alleged “Antifa” activities after President Trump designated the umbrella term a ter...

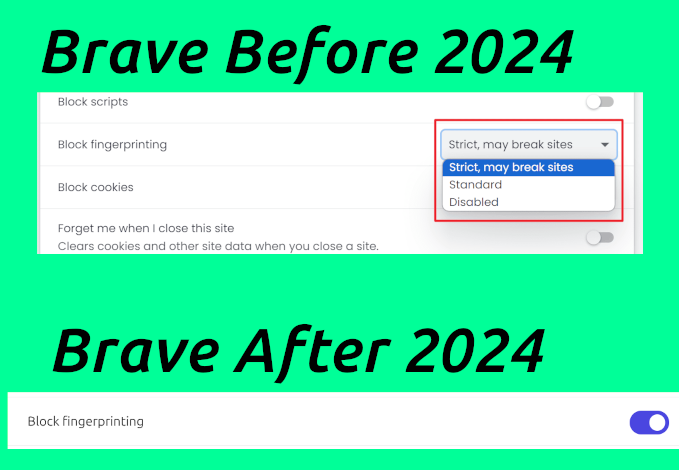 Tor Browser attempts to hide unique screen sizes by blocking and restricting Javascript, which causes services such as Google, Reddit, and Cloudflare to haze you.
That's why I'm excited about HydraVeil's feature to instantly create a new display, that realistically looks to websites like the browser window is your computer's full screen dimensions. Here we can see deviceinfo-me compare Tor Browser to HydraVeil's profiles, and it does not percieve it to be spoofed.
Tor Browser attempts to hide unique screen sizes by blocking and restricting Javascript, which causes services such as Google, Reddit, and Cloudflare to haze you.
That's why I'm excited about HydraVeil's feature to instantly create a new display, that realistically looks to websites like the browser window is your computer's full screen dimensions. Here we can see deviceinfo-me compare Tor Browser to HydraVeil's profiles, and it does not percieve it to be spoofed.
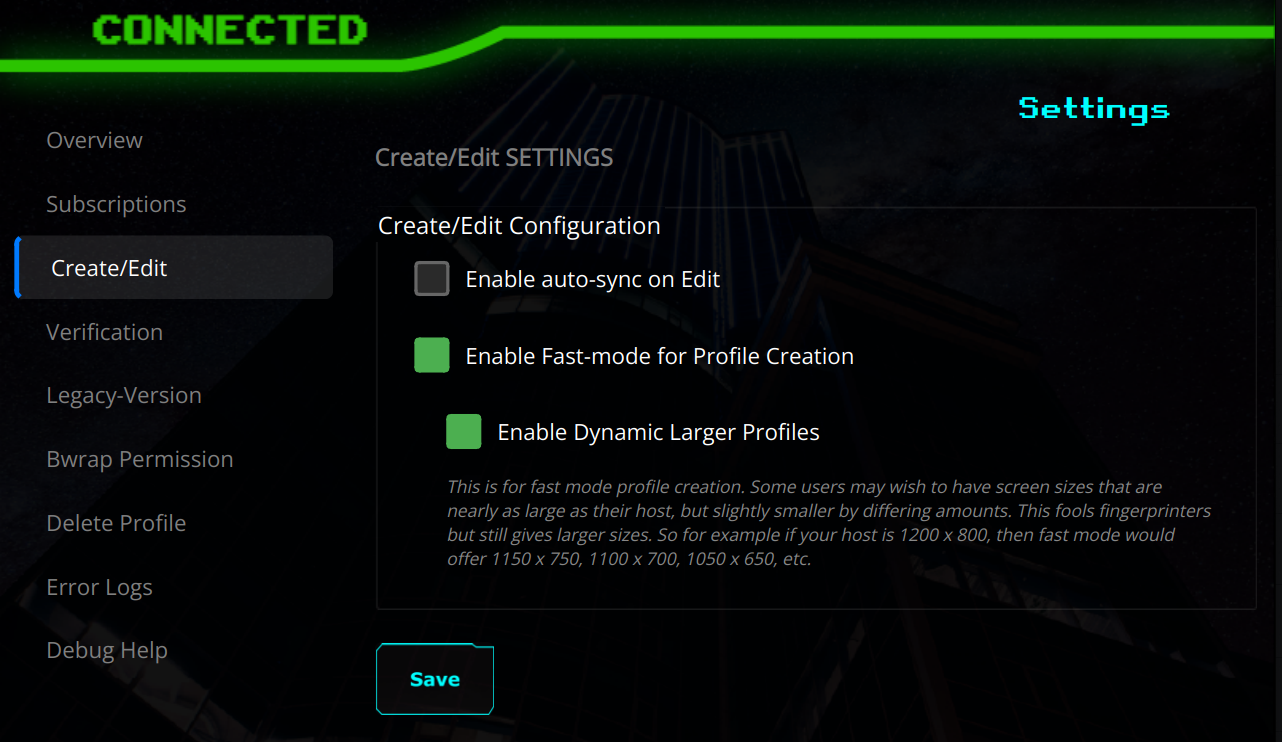
 But many HydraVeil users have complained that they don't want to deal with smaller windows. And that's why I'm excited about our new update today.
We are proud to present a new 'dynamic mode' for quick profile creation, which when enabled, presents many screen size options that are only slightly smaller than your host, in 50 dimension increments. This allows the user to effortlessly and conveniently get profiles that comfortably fill up their host’s display window, but each one is slightly different to fingerprinters.
But many HydraVeil users have complained that they don't want to deal with smaller windows. And that's why I'm excited about our new update today.
We are proud to present a new 'dynamic mode' for quick profile creation, which when enabled, presents many screen size options that are only slightly smaller than your host, in 50 dimension increments. This allows the user to effortlessly and conveniently get profiles that comfortably fill up their host’s display window, but each one is slightly different to fingerprinters.
 Learn more from our release notes:
Learn more from our release notes:
 Linux is flawed and any app can abuse the DBUS to rip down your VPN without any elevated privileges. To prove this, today our team presents both an original demo attack script to break through Mullvad & Proton, however these same concepts can apply to many others.
But there is no point in complaining, if you aren't going to do anything about it. And that's why I'm proud of our team to work so many sleepless nights and come through. We've already pushed to HydraVeil's distro, an original solution, that presents a much stronger resistance to these type of network interface attacks, but without any of the downside burdens of a virtual machine.
The link below has:
-5-min Demo Video w/ an easy to follow explanation
-Article version of the video
-FOSS script
-Solution already pushed to HydraVeil
But all the technology in the world, isn't going to do any good, if nobody is going to use it. That's true not just for our team's app, but building up all of Nostr.
That's why I'm asking for your help. Spend a few minutes looking at our materials. I've made it as easy to comprehend as possible. Realize it is real. And when you do, share & repost it.
Linux is flawed and any app can abuse the DBUS to rip down your VPN without any elevated privileges. To prove this, today our team presents both an original demo attack script to break through Mullvad & Proton, however these same concepts can apply to many others.
But there is no point in complaining, if you aren't going to do anything about it. And that's why I'm proud of our team to work so many sleepless nights and come through. We've already pushed to HydraVeil's distro, an original solution, that presents a much stronger resistance to these type of network interface attacks, but without any of the downside burdens of a virtual machine.
The link below has:
-5-min Demo Video w/ an easy to follow explanation
-Article version of the video
-FOSS script
-Solution already pushed to HydraVeil
But all the technology in the world, isn't going to do any good, if nobody is going to use it. That's true not just for our team's app, but building up all of Nostr.
That's why I'm asking for your help. Spend a few minutes looking at our materials. I've made it as easy to comprehend as possible. Realize it is real. And when you do, share & repost it.
 What is it:
A Decentralized VPN run by Nostr Operators, with a Linux client that cryptographically verifies the node operator on connection.
Upsides:
–Earn Bitcoin or Monero
–No upfront cost
–Help Nostr
–Help Privacy
–Be Part of Innovation
–Grow a Parallel Economy
–Have Meaning and Purpose
–Continue to Earn off a one-time Setup.
Low Burdens:
–Low Time Commitment (1 hour)
–No Legal Risk, no-KYC Datacenters
–No Financial Cost to You
–No Stake Requirement
–No Inserting Your Nsec Into New Apps. You can use the Nostr client you already have now.
–Low Technical Risk
–Well established protocols (Wireguard, id_ed25519 keys, openssl)
–It’s a Docker Image, an automated script is pulling it for you.
–We Provide Full Support to You & the Customers
–Get Free Linux Opsec Tips With Hands On Experience from our Team.
Learn more:
What is it:
A Decentralized VPN run by Nostr Operators, with a Linux client that cryptographically verifies the node operator on connection.
Upsides:
–Earn Bitcoin or Monero
–No upfront cost
–Help Nostr
–Help Privacy
–Be Part of Innovation
–Grow a Parallel Economy
–Have Meaning and Purpose
–Continue to Earn off a one-time Setup.
Low Burdens:
–Low Time Commitment (1 hour)
–No Legal Risk, no-KYC Datacenters
–No Financial Cost to You
–No Stake Requirement
–No Inserting Your Nsec Into New Apps. You can use the Nostr client you already have now.
–Low Technical Risk
–Well established protocols (Wireguard, id_ed25519 keys, openssl)
–It’s a Docker Image, an automated script is pulling it for you.
–We Provide Full Support to You & the Customers
–Get Free Linux Opsec Tips With Hands On Experience from our Team.
Learn more: