A Technical Analysis of the #Nostr Protocol 🤙🏻
#grownostr #security #privacy #analysis
Nostr is an emerging protocol that allows users to publish short messages called "events" in a decentralized, censorship-resistant, and cryptographically verifiable manner. It has the potential to enable privacy-focused social networking and web3 applications.
This analysis examines Nostr's technical design, highlighting key components, vulnerabilities, and areas needing improvement. It is intended for readers with a passing knowledge of cryptography, networks, and blockchain technology. Casual users may find some sections challenging, but I aim to reward patient, focused reading with deep insights into this novel protocol.
# Overview 💻
Nostr utilizes digital signatures and public-key cryptography to authenticate events published by users. Users generate a private/public key-pair, registering their public key on the network. This key serves as their identity. Users sign events with their private key before publishing to relays. Relays then distribute the events across the network. Clients can verify event integrity via the signatures.
This high-level architecture offers censorship resistance and verifies event provenance. However, complex challenges emerge when examining Nostr's design through a technical lens.
# Cryptographic Foundations 🔒
Nostr identities are generated as secp256k1 key-pairs. This offers compatibility with external systems like Bitcoin and Ethereum which utilize the same curve. Key-pairs are generated on the client side, ideally using a secure random number generator with sufficient entropy.
Once generated, the key-pair should never be transmitted. The private key in particular must be kept secret. Nostr clients are thus responsible for properly securing keys. Future clients should support encrypted local storage, multi-factor access control, and seed phrase backups. Weaknesses here compromise identity ownership.
All Nostr events are signed with Schnorr signatures using the author's private key. Schnorr offers a space-efficient signing algorithm but relies heavily on random nonce generation. Poor entropy pools during signing open the door to compromise via nonce-reuse.
Fortunately, the nonce is not revealed on-chain, limiting exploitability. Nonetheless, clients should implement RFC 6979 deterministic nonce generation. This eliminates randomness as an attack vector.
# Sybil Resistance 🫂
Nostr's open design allows anyone to generate a key-pair and immediately participate. There is no imposed cost-of-entry or identity verification preventing Sybil attacks — a weakness compared to systems like Bitcoin.
A single actor could trivially generate millions of identities. Combined with Nostr's re-posting mechanics, this amplifies the potential scale of disinformation campaigns. Similar techniques have been exploited on social platforms like Twitter.
Nostr currently lacks robust Sybil resistance. Possible mitigations include rate-limiting new key generation, requiring Proof-of-Work, and leveraging Web-of-Trust style reputation systems. Careful design is needed to prevent undue centralization.
# Metadata Privacy 📝
By default, Nostr events are publicly accessible. They contain metadata including the author's public key. Clients can correlate events across relays to profile users. This reduces privacy, especially for less tech-savvy users unaware of the risks.
Future Nostr clients should make pseudonymous and encrypted usage easy. Predefined "personas" with distinct keys, ephemeral keys, mix networks, and metadata stripping should become standard privacy tools.
However, blindly encrypting all content poses discoverability challenges. Search, filtering, and network analysis rely on accessible metadata. There are open research questions around balancing privacy and utility.
# Censorship Resistance 📛
Nostr's decentralized architecture should make censorship technically challenging. There is no central entity that can eradicate content or ban users.
However, Nostr's relay infrastructure poses centralization risks. A handful of large relays could potentially collude to censor events or de-platform targets. Nostr needs robust incentives for relay operators to prevent oligopolies.
Censorship at the relay level also remains an open challenge. Existing systems like Secure Scuttlebutt explore concepts like relay "matchmaking" and sharding events across diverse relay groups.
# Spam Prevention 📬
Nostr's public nature makes it vulnerable to spam. Computational Proof-of-Work and fee mechanisms have been proposed but neither is foolproof. Clever anti-spam that resists censorship and gaming remains an open research problem.
Basic rate-limiting on new key registration, events published, and introductions sent helps but is trivial to circumvent. More advanced techniques like fees weighted by account reputation, staking mechanisms, and selectively applying Proof-of-Work based on risk factors warrant exploration.
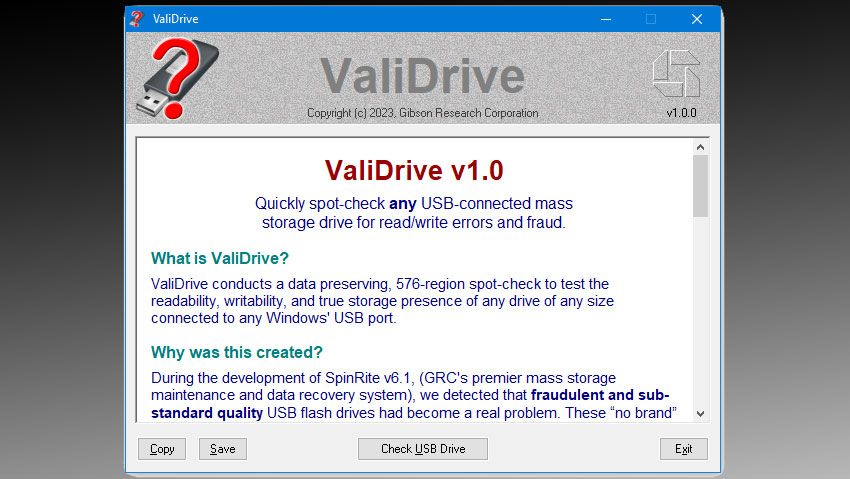
# Secure Key Management 🔐
Nostr's security model depends on users properly managing private keys. If users select weak passwords or store keys improperly, malicious actors can compromise their identities.
This poses an enormous challenge given that most users lack crypto-security knowledge. Nostr clients should implement multi-factor authentication, encrypted local storage, and easy-to-use backups like seed phrases. Usability testing is critical — security mechanisms that seem too complex may be ignored or circumvented by users.
Platforms like Keybase demonstrate the difficulty of making key management accessible. Nostr clients should learn from past efforts while recognizing the uniquely sensitive nature of social networking data.
# Scalability 📈
Nostr's throughput is limited by its relay infrastructure. Early testing suggests relays can comfortably handle 2000 events per second. Further optimizations like compression, sharding, and efficient routing algorithms will help.
But fundamental scalability limitations remain. Relays are constrained by bandwidth, storage, and real-time event processing. As adoption grows, demand may overwhelm relay capacity. Possible mitigations include sharding the network into relay clusters and introducing client-side caching.
Incentivizing a robust relay network is critical for scalability. Nostr currently lacks effective incentives for operating high-capacity relays. Ongoing research into decentralization-compatible business models is essential as utilization increases.
# Conclusion 👨🏻💼
This analysis reveals that while Nostr offers a novel approach to decentralized social networking, complex technical challenges remain. Sybil resistance, metadata privacy, censorship resistance, spam prevention, key management, and scalability all warrant additional research and protocol evolution.
Nonetheless, Nostr represents a promising step forward in an era of centralized platforms and compromised user rights. With transparent analysis of its strengths and weaknesses, collaborative research, and responsible protocol design, Nostr may yet fulfill its aspirational goal of user empowerment. The road ahead will require vigilance, creativity, and a commitment to the open, decentralizing ideals which motivate this project.