The Nixpkgs PR for Sparrow 1.8.5 is now available:  I also added build-time GPG verification using npub1hea99yd4xt5tjx8jmjvpfz2g5v7nurdqw7ydwst0ww6vw520prnq6fg9v2 public key.
:)
I really like the idea that if it builds, then it's also verified. Damn, Nix is awesome!
It's also possible to get the update now, by getting it from my repo: $ nix run github:emmanuelrosa/erosanix#sparrow
BUT, the Nixpkgs in my repo doesn't have HWI 3.0; HWI was updated to 3.0 in Nixpkgs about 4 days ago. Sparrow should still work fine with HWI 2.4, as long as you're not trying to use an emulated hardware wallet. See
I also added build-time GPG verification using npub1hea99yd4xt5tjx8jmjvpfz2g5v7nurdqw7ydwst0ww6vw520prnq6fg9v2 public key.
:)
I really like the idea that if it builds, then it's also verified. Damn, Nix is awesome!
It's also possible to get the update now, by getting it from my repo: $ nix run github:emmanuelrosa/erosanix#sparrow
BUT, the Nixpkgs in my repo doesn't have HWI 3.0; HWI was updated to 3.0 in Nixpkgs about 4 days ago. Sparrow should still work fine with HWI 2.4, as long as you're not trying to use an emulated hardware wallet. See  #nixos #nix
#nixos #nix
GitHub
sparrow : 1.8.4 -> 1.9.0 by emmanuelrosa · Pull Request #303393 · NixOS/nixpkgs
Description of changes
This PR contains three commits:
Version bump of sparrow from 1.8.4 to 1.9.0.
Migration from stdenv to stdenvNoCC
GPG verif...
GitHub
Release 3.0.0 · bitcoin-core/HWI
Also available on PyPi and can be installed with pip install -U hwi
Added
--emulators option to enumerate and detect emulators. Otherwise default ...
 In the example above, I simply replaced the correct public key (which is contained in the erosanix repo for reproduceability) with my own to cause an intentional failure.
The end result is that the end-user can have limited confirmation that if Bisq2 installs, then the installation is verified.
I believe this form of verification is superior to what I had done before, which is to automatically or manually verify the .deb; In this form, the end user has absolutely no confirmation that the .deb file has been verified.
I say "limited confirmation" because this doesn't completely absolve the user's responsibility to verify the download. For example, a malicious actor can replace the public key and source files that are in the repo. I haven't fully developed the end-user verification process, but I think it could be something like this:
1. Audit the Nix expression to understand that in fact the .dep package is being verified and no funny business is happening.
2. Compare the public key that's in the repo with the one on the Bisq website to confirm they are the same.
3. To make the process quicker in the future, use your own GPG key to create external signatures for the public key (in the repo) and the Nix expression.
I'd have to modify the Nix expression a bit, but the idea is that once the code has been audited and signed, future verification can be done quickly by verifying the Nix expression and public key with the signatures. To make this work I need to store the Bisq2 version and the SHA256 checksums in a separate Nix file.
In the example above, I simply replaced the correct public key (which is contained in the erosanix repo for reproduceability) with my own to cause an intentional failure.
The end result is that the end-user can have limited confirmation that if Bisq2 installs, then the installation is verified.
I believe this form of verification is superior to what I had done before, which is to automatically or manually verify the .deb; In this form, the end user has absolutely no confirmation that the .deb file has been verified.
I say "limited confirmation" because this doesn't completely absolve the user's responsibility to verify the download. For example, a malicious actor can replace the public key and source files that are in the repo. I haven't fully developed the end-user verification process, but I think it could be something like this:
1. Audit the Nix expression to understand that in fact the .dep package is being verified and no funny business is happening.
2. Compare the public key that's in the repo with the one on the Bisq website to confirm they are the same.
3. To make the process quicker in the future, use your own GPG key to create external signatures for the public key (in the repo) and the Nix expression.
I'd have to modify the Nix expression a bit, but the idea is that once the code has been audited and signed, future verification can be done quickly by verifying the Nix expression and public key with the signatures. To make this work I need to store the Bisq2 version and the SHA256 checksums in a separate Nix file.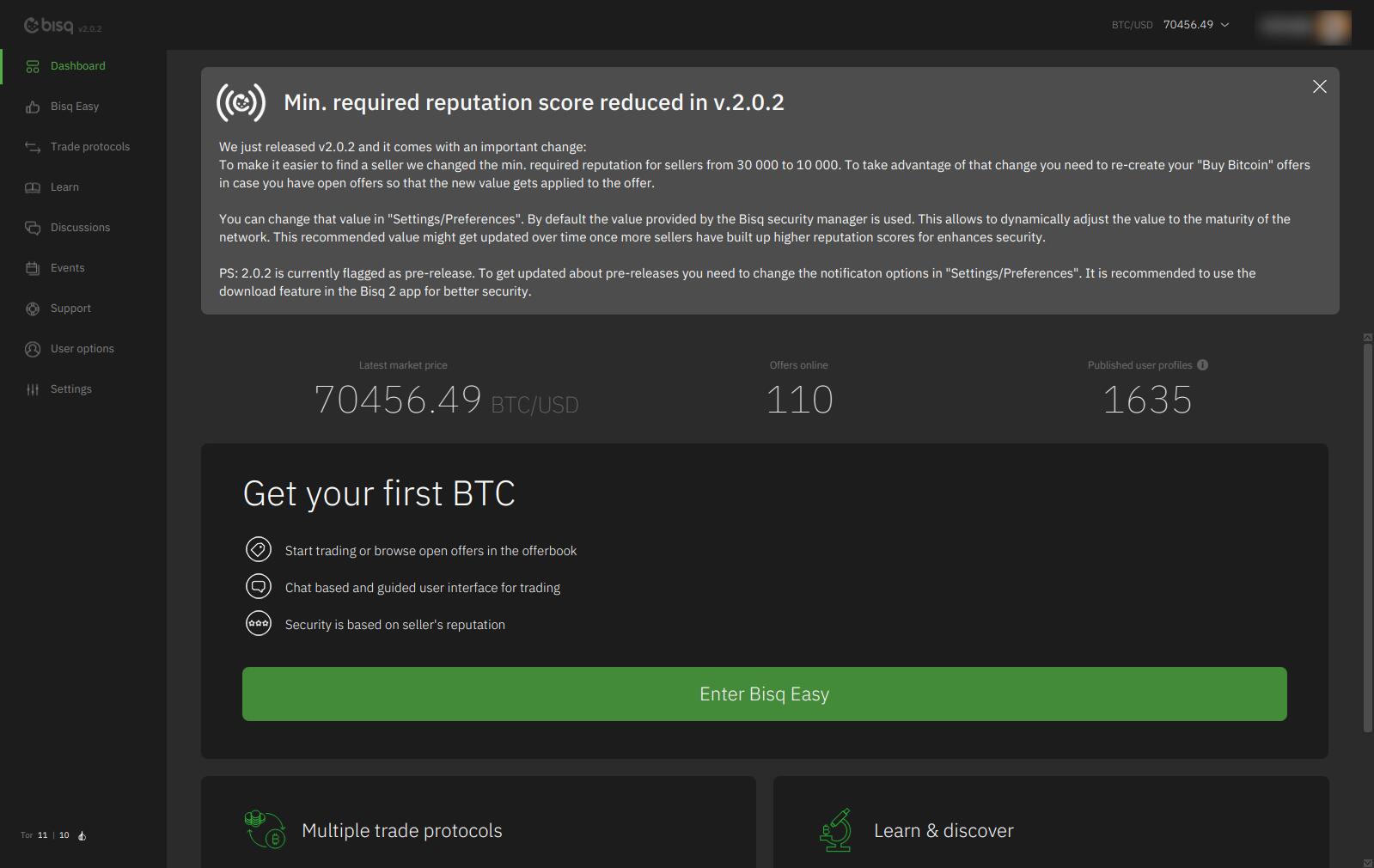 $ nix run github:emmanuelrosa/erosanix#bisq2
#bisq1 #nix #nixos
$ nix run github:emmanuelrosa/erosanix#bisq2
#bisq1 #nix #nixos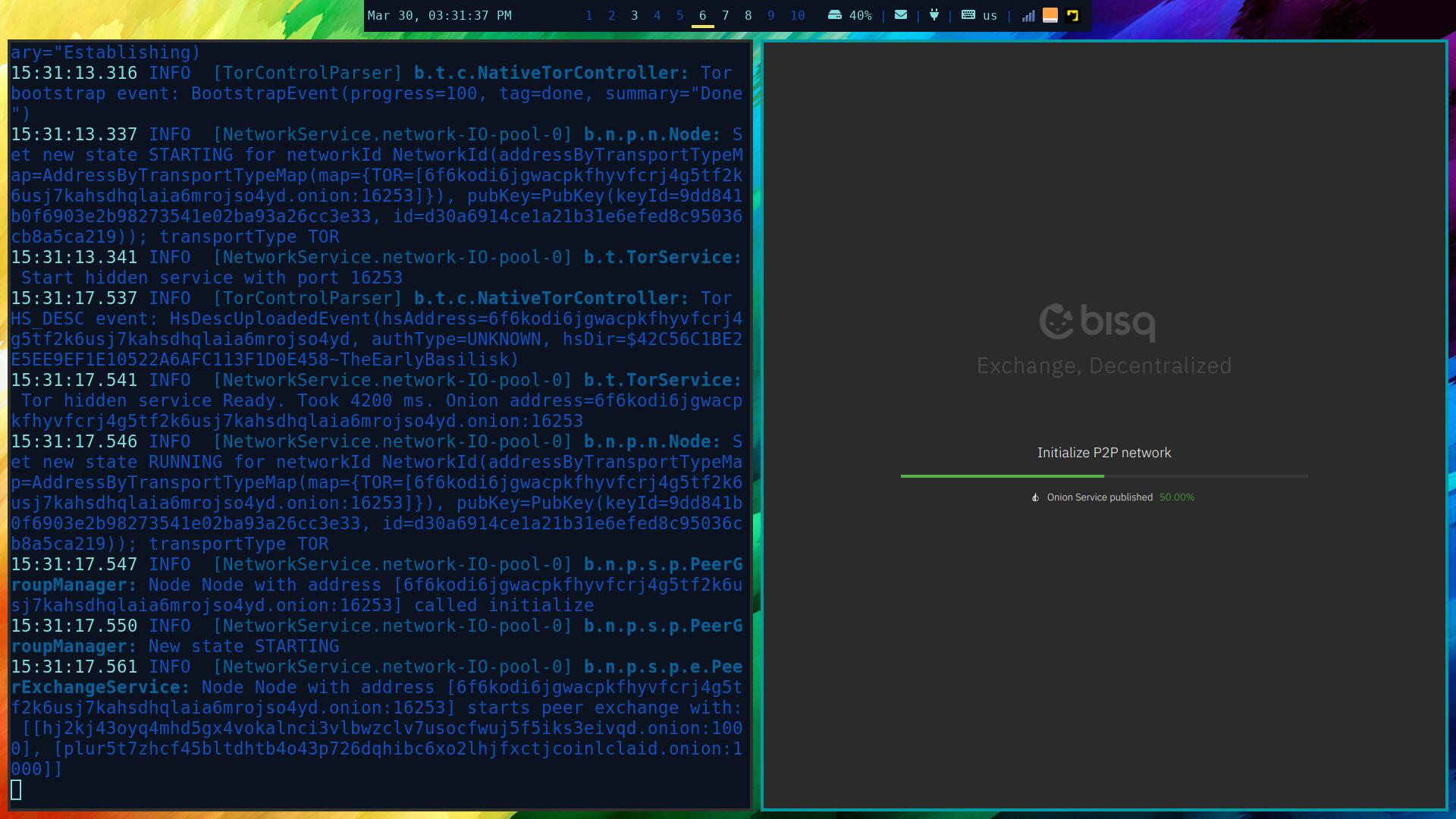 Perhaps it's a network issue on my side.
If you want to give it a go, run: nix run github:emmanuelrosa/erosanix#bisq2
If you have a 4K display, then you way want to use this:
$ nix shell github:emmanuelrosa/erosanix#bisq2
$ bisq2-hidpi
#nixos
Perhaps it's a network issue on my side.
If you want to give it a go, run: nix run github:emmanuelrosa/erosanix#bisq2
If you have a 4K display, then you way want to use this:
$ nix shell github:emmanuelrosa/erosanix#bisq2
$ bisq2-hidpi
#nixos #nix #nixos #memestr
#nix #nixos #memestr