How’s that Strategic Bitcoin Reserve coming?

GHOST
ghost@nostrplebs.com
npub18dlu...h8x3
Operational privacy for real people.
Just because your VPN status says connected doesn’t mean you’re covered.


Untraceable Digital Dissident
Check VPN Leaks Before Trusting Connected
Learn how to test VPN leaks across startup, reconnects, DNS, IPv6, and browser behavior so a clean final state doesn't fool you.
Probably nothing
https://substr.network/s/privacy
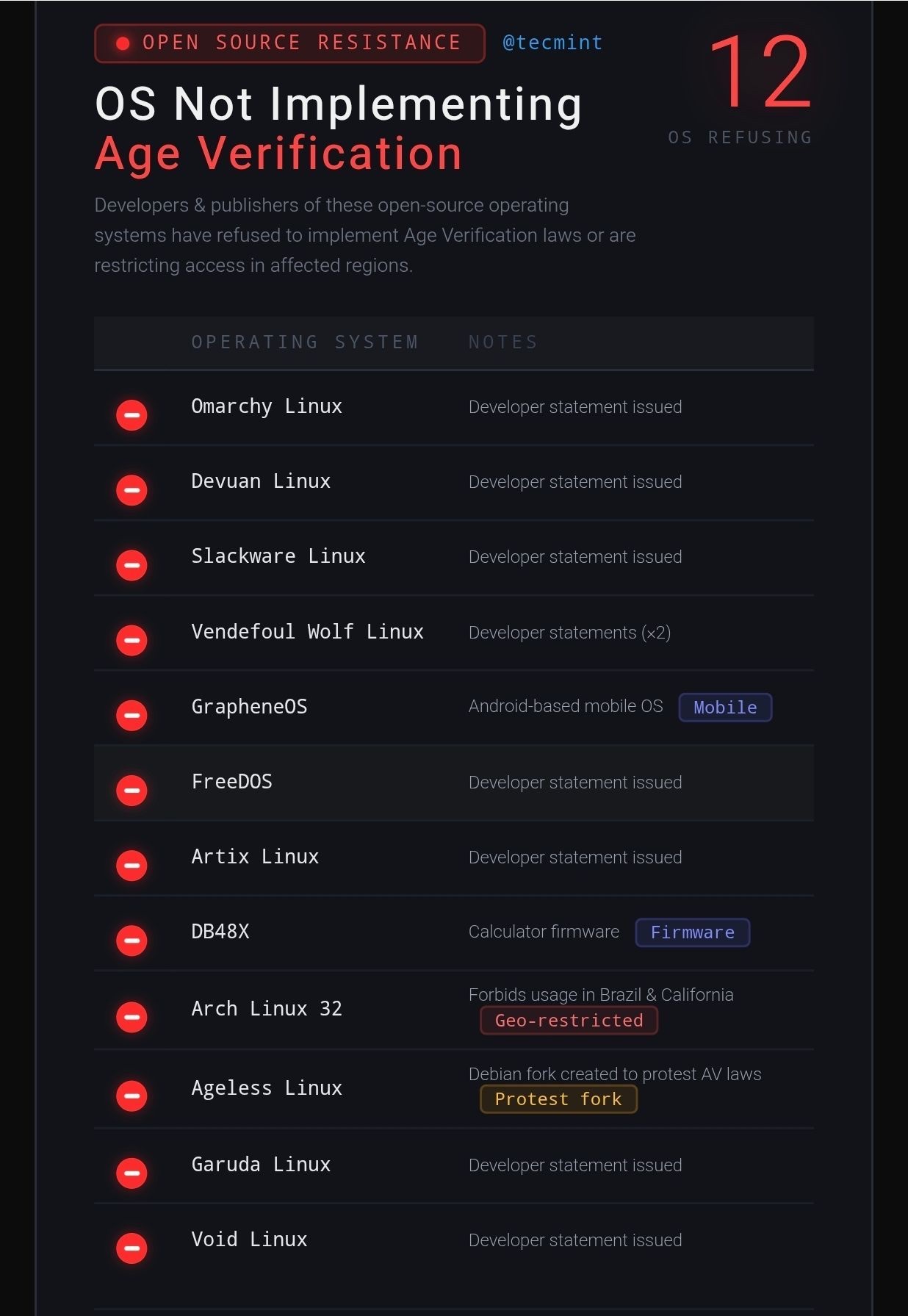
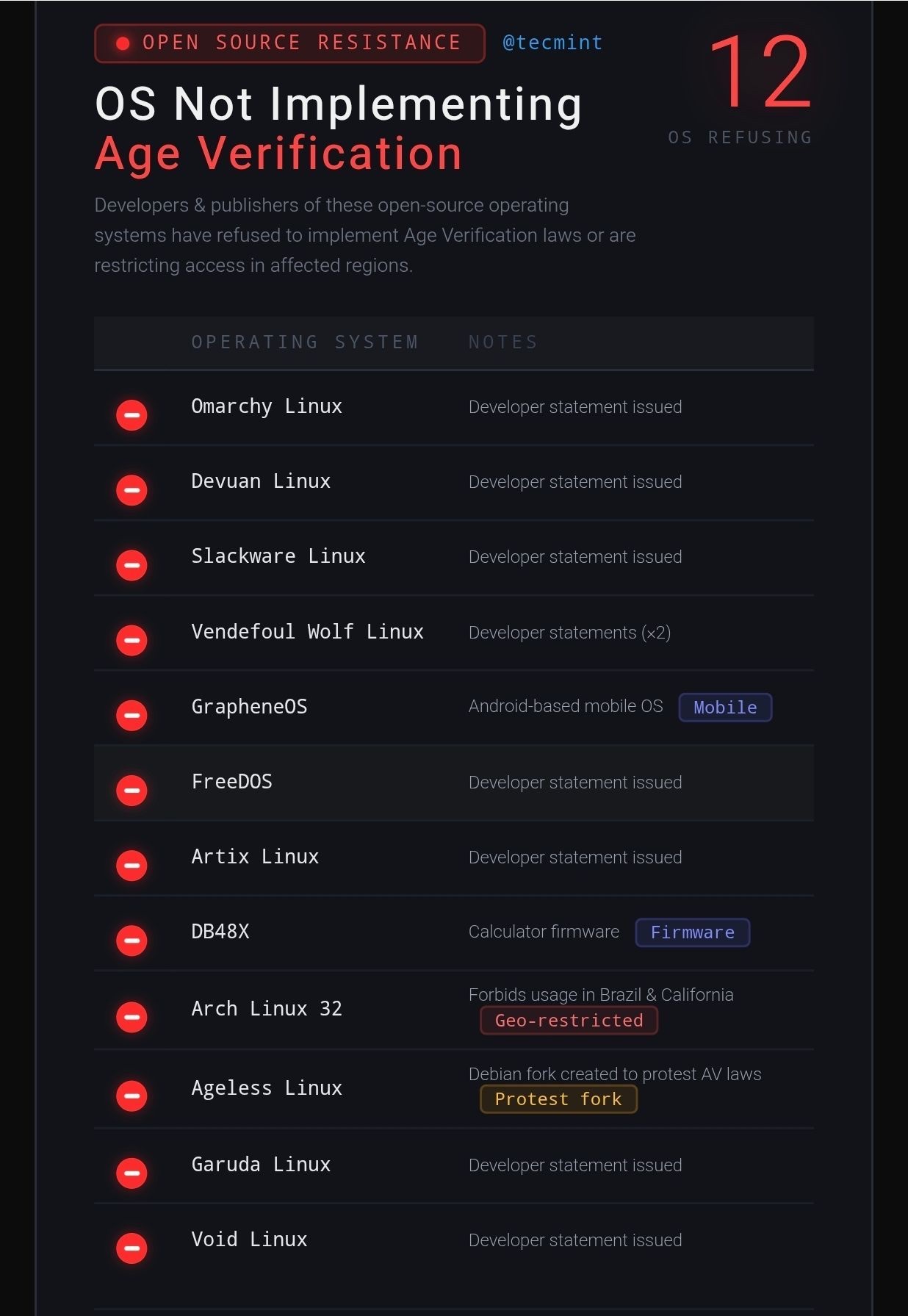
How closely are you watching the OS age verification laws?

Wen mobile app?
**bold text**
Families have different DNS needs than just ad blocking
Most families don't need a more aggressive DNS blocklist.
They need a smarter one.
Block porn, scams, phishing, and malware with category filtering first. Then add a stable list like OISD so you don't break the whole house.


Untraceable Digital Dissident
Best DNS Filter for Families: Block Porn, Scams, and Malware Without Breaking the House
Looking for the best DNS blocklist for families? This guide shows how to block porn, scams, phishing, and malware using category based DNS filterin...
Your phone number is not just for calls and texts.
It becomes login recovery, contact discovery, account matching, and the quiet thread connecting services that should stay separate.
That's the real problem.
A lot of people harden the phone, tweak settings, and install privacy apps, while leaving the number as the one clean link tying everything together.
So the phone looks quieter.
But the identity layer is still loud.
That is why I created the Phone Number Containment Guide.
This is a practical guide for reducing how much power your phone number has over your digital life without wrecking daily use.
Inside, you’ll learn how to:
* separate an operational number from a recovery number
* reduce number based account linkage
* audit which apps and services have your number
* clean up cross contamination between identities
* build a setup you can actually maintain
You also get:
* Quick Start Containment Plan
* One Page Containment Checklist
* App Exposure Audit Worksheet
* Recovery Separation Planner
* Mini Course with infographics
This is not a purity test or a burner phone fantasy.
It is a practical system for people who still need a phone, still need accounts, and still want tighter control over how their number gets used.
A phone number should be a tool.
Not your identity spine.
Get the Phone Number Containment System here:


Untraceable Digital Dissident
L2: Phone Number Containment Guide – Untraceable Digital Dissident
Stop Your Number From Exposing You How to Use a Phone Without Letting the Number Become Your Identity Your phone number is not just for calls and t...
Most families don't need a more aggressive DNS blocklist.
They need a smarter one.
Block porn, scams, phishing, and malware with category filtering first. Then add a stable list like OISD so you don't break the whole house.


Untraceable Digital Dissident
Best DNS Filter for Families: Block Porn, Scams, and Malware Without Breaking the House
Looking for the best DNS blocklist for families? This guide shows how to block porn, scams, phishing, and malware using category based DNS filterin...


False confidence is a privacy risk.
If you have not checked your resolver path, VPN exit, IPv6 handling, browser exposure, and router behavior, you don't really know if your setup is working.
Here is a 15 minute checklist to audit it fast.


Untraceable Digital Dissident
Network Privacy Audit: Find Your First Failure
Run a 15 minute network privacy audit to find whether DNS, VPN, browser, device, or router fails first and move to the right fix.

